
Risk Assessment for Substation Automation Systems
Share
Modern power grids rely on Substation Automation Systems (SAS) to ensure reliable and efficient electricity flow. These systems integrate high-voltage components (like transformers) with low-voltage technologies (like Intelligent Electronic Devices) to perform critical tasks such as control, monitoring, and voltage regulation. However, their interconnected nature introduces vulnerabilities, especially in cybersecurity.
Key takeaways:
- Why it matters: SAS improves grid reliability but exposes systems to risks like cyberattacks, equipment damage, and operational errors.
- Risk areas: Personnel safety, financial loss, service interruptions, and equipment reliability.
- Assessment tools: Standards like ISA/IEC 62443 and frameworks like OCTAVE Allegro help identify threats, evaluate vulnerabilities, and prioritize risks.
- Mitigation strategies: Redundant systems, secure communication protocols, and regular maintenance reduce risks.
This article provides actionable steps to safeguard SAS, ensuring compliance with standards like ISO 27001 while maintaining grid stability.
Substation Automation Systems Risk Assessment Framework and Mitigation Steps
Cyber Physical Security Analysis of Digital Substations
sbb-itb-501186b
Components of Risk Assessment Frameworks
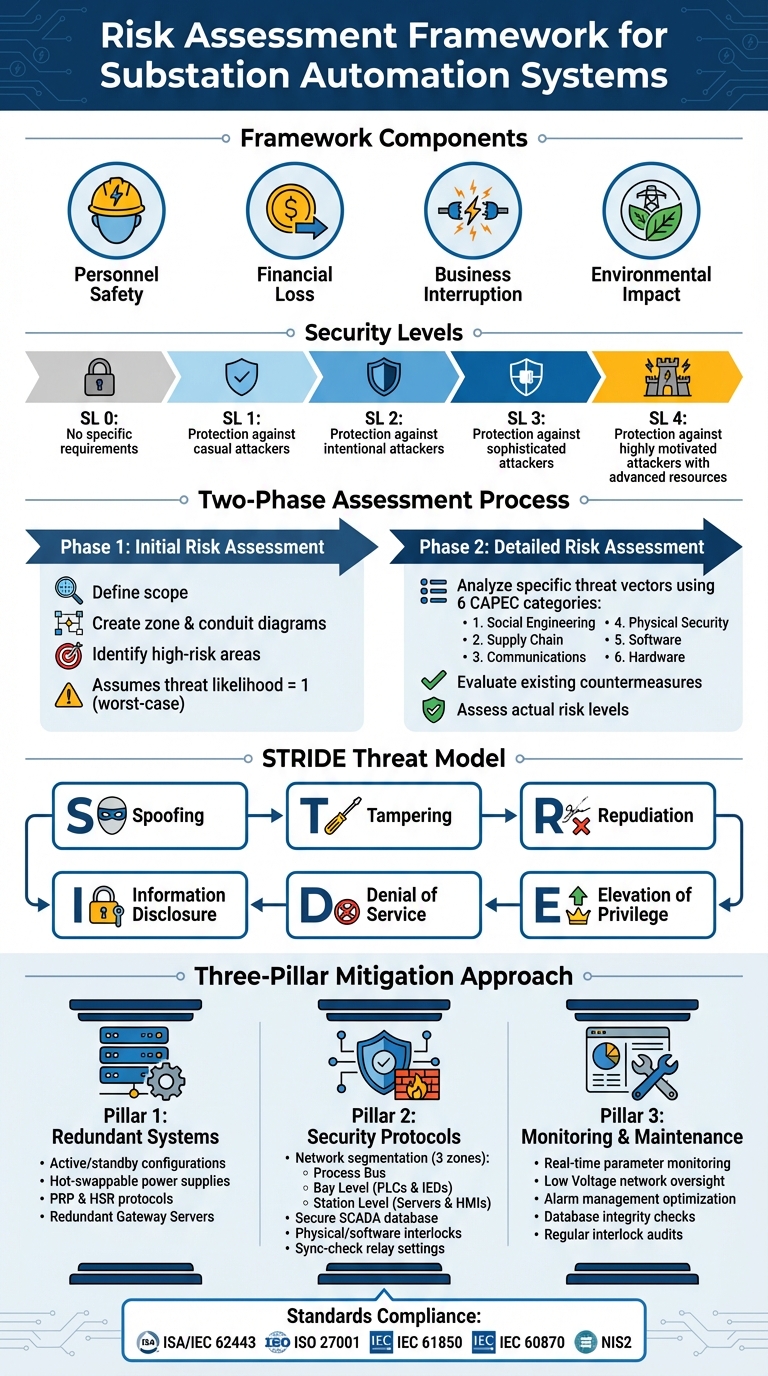
A solid SAS risk assessment framework is built on three key components. The ISA/IEC 62443-3-2 standard, particularly Zone and Conduit Requirement 5 (ZCR 5), forms the backbone of this approach. It differentiates between Zones (grouped assets based on criticality or function) and Conduits (communication channels connecting these zones). This structure ensures each area receives the proper analysis it needs. These components tie directly to the cybersecurity challenges and vulnerabilities mentioned earlier, creating a structured way to address SAS risks.
The framework assesses risks across four main areas: personnel safety, financial loss, business interruption, and environmental impact. Risks are evaluated against defined Security Levels (SL), ranging from SL 0 (no specific requirements) to SL 4 (defense against highly motivated attackers with advanced resources). As highlighted in the International Journal of Information Security:
"The ISA/IEC 62443 series of standards is suited for the design and security risk analysis of IACS, and has been submitted to the International Standards on Auditing and International Electrotechnical Commission for global adoption as international standards".
These foundational elements set the stage for detailed methodologies in identifying threats and analyzing vulnerabilities.
Identifying Potential Threats
The first step in identifying threats involves creating Data Flow Diagrams (DFDs) to map out all data flows and network connections within the system. These diagrams help pinpoint trust boundaries and potential attack points. Using the STRIDE methodology, threats are categorized into six types: Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege. These categories align with critical security properties like authentication, integrity, and availability.
A Threat and Operability (THROP) analysis takes this a step further by incorporating insights from asset owners, who bring valuable operational context to the process. This analysis looks at specific components of substation automation systems, such as SCADA servers, Gateway servers, Operator Workstations (OS), and Engineering Workstations (ES). For example, Engineering Workstations pose a particularly high risk because they program IEDs and PLCs. Unauthorized access here could lead to dangerous changes in interlocks or protection thresholds.
Once threats are identified, the focus shifts to evaluating vulnerabilities within communication channels.
Evaluating System Vulnerabilities
Vulnerability assessment involves scanning for Common Vulnerabilities and Exposures (CVEs) and aligning them with threat categories using tools like the Common Weakness Enumeration (CWE) and the National Vulnerability Database (NVD). Each system level - Process, Bay, and Station - has unique vulnerabilities that need to be prioritized based on their severity. For instance, if delta-frequency thresholds in sync-check relays are incorrectly set, it could lead to equipment damage by connecting mismatched frequencies.
Cybersecurity consultant Dietmar Marggraff underscores another critical risk:
"If the operator does not receive the correct information on their HMI, they may perform incorrect control actions. This may include switching more circuits onto a bus than it can handle resulting in an over-load condition".
Operator Workstations, for example, often trust the system database without question. If this database is compromised, operators could act on false information, potentially causing unsafe manual control actions. To address this, vulnerabilities must be prioritized based on their severity relative to each zone's target Security Level.
With vulnerabilities mapped out, the next step involves assessing the impact and likelihood of these threats.
Analyzing Impact and Likelihood
Accurately estimating both the impact and likelihood of threats is essential. Asset owners and system integrators need to identify critical attack paths and select countermeasures tailored to those risks. By referencing ISA/IEC 62443-3-3 requirements, they can choose measures that maximize security while efficiently allocating resources.
Alarm management risks, such as alarm flooding (overwhelming operators with false alerts) or alarm suppression (hiding genuine error conditions), must also be considered. These issues can delay critical interventions. Each risk scenario should be evaluated across the four main impact areas - personnel safety, financial loss, business interruption, and environmental impact - using likelihood ratings that reflect the system's current state and the sophistication of potential attackers.
Risk Assessment Methodologies
Standardized methodologies provide a clear and structured way to evaluate risks, especially when addressing threats and vulnerabilities. One widely recognized standard for assessing cybersecurity risks in industrial automation, particularly in substation automation systems (SAS), is the ISA/IEC 62443-3-2 framework. This standard organizes the process into two main phases: Initial Risk Assessment and Detailed Risk Assessment.
The Initial Risk Assessment focuses on defining the scope, creating zone and conduit diagrams, and identifying high-risk areas. This phase assumes a threat likelihood of one to evaluate the worst-case scenarios. As Patrick O'Brien from exida explains:
"The fundamental method behind the Initial Risk Assessment is that it assumes a threat likelihood of one and focuses on evaluating the worst-case scenario if a cyber asset is compromised".
This approach is particularly useful for prioritizing zones that require further analysis. It also supports strategies like network segmentation, where devices with similar security needs are grouped and isolated using tools such as firewalls or data diodes.
The Detailed Risk Assessment takes a closer look at specific threat vectors and existing countermeasures. Instead of analyzing an overwhelming number of potential threats, it uses the CAPEC database to group threats into six categories: Social Engineering, Supply Chain, Communications, Physical Security, Software, and Hardware. This categorization simplifies the process, allowing plant personnel to incorporate their operational knowledge without becoming bogged down by technical complexities. It also evaluates protections like firewalls, managed switches, intrusion detection systems, and logic solvers to assess the actual risk level.
While the ISA/IEC framework provides a phased approach to quantifying system risk, other methodologies, such as OCTAVE Allegro, offer an alternative perspective. Developed by the Software Engineering Institute, OCTAVE Allegro is an asset-focused framework designed for organizations seeking a self-directed process. It emphasizes the management of individual information assets - like IED configurations, SCADA databases, and HMI interfaces - by examining how they are stored, transported, and processed across "containers" (people, technology, and facilities).
This framework follows eight structured steps, starting with the establishment of risk measurement criteria and ending with the selection of mitigation strategies. Standardized worksheets guide each step, ensuring consistency throughout the process. By focusing on specific information assets, OCTAVE Allegro complements the ISA/IEC approach, broadening the scope for effective risk management.
Risk Mitigation Strategies
Once risks have been assessed, the next step is to take actionable steps to address them. Mitigation efforts typically focus on three key areas: creating redundancy in critical systems, securing communication networks, and maintaining constant oversight through monitoring and maintenance.
Designing Redundant Systems
Redundancy is a cornerstone of risk mitigation, as it helps prevent single points of failure in critical substation components. For instance, modern systems often use active/standby setups, where a standby unit automatically takes over if the active one fails. This is particularly crucial for components like Remote Terminal Units (RTUs), Human-Machine Interfaces (HMIs), and power supplies - hardware that is especially prone to failure in substation environments.
Gateway servers should also be configured redundantly to ensure remote access remains available, even if one server goes offline. To make repairs easier, power supplies should be designed as hot-swappable from the front, allowing technicians to replace them without shutting down the system.
For network reliability, protocols like PRP (Parallel Redundancy Protocol) and HSR (High-availability Seamless Redundancy) are vital. These ensure uninterrupted communication, even in the event of a failure, which is critical in scenarios where milliseconds make a difference. Ray Wright from NovaTech, LLC underscores the importance of this approach:
"The failure of one portion of the system should not cause a failure in another portion of the system".
When implementing redundancy, ensure that operator actions, such as tagging and alarm acknowledgments, are mirrored between active and standby units. Regular diagnostic checks on standby units are also necessary to confirm their readiness, including monitoring temperature, power status, and time synchronization.
Implementing Security Protocols
Alongside redundancy, strong security measures are essential for minimizing risks. One effective strategy is network segmentation, dividing Substation Automation Systems into zones: the Process Bus (linking process and bay levels), the Bay Level (housing PLCs and IEDs), and the Station Level (including servers, HMIs, and remote connections). This structure limits how far a breach can spread and simplifies access control.
Securing the SCADA database is another priority to prevent erroneous control actions. Engineering Workstations must also be locked down, as misconfigurations can disrupt system behavior.
Physical and software interlocks add an extra layer of safety by enforcing specific conditions before control actions can proceed. For example, sync-check relays should have strict settings for phase, voltage, and frequency to prevent damage from mismatched connections. Common configurations - like "Hot Bus - Dead Line" or "Hot Line - Hot Bus" - should remain within safe operating ranges.
For remote access, Gateway Servers act as secure entry points, translating protocols while safeguarding connections to remote control centers. Regularly cross-checking HMI data with physical field measurements ensures operators aren't misled by inaccurate or spoofed information.
Regular Maintenance and Monitoring
Real-time parameter monitoring - tracking voltage, power, current, and temperature - provides a clear picture of substation conditions, enabling operators to catch potential issues early.
Low Voltage (LV) networks, which power IEDs, relays, and control systems, require constant oversight. As Marggraff points out:
"The SAS needs to monitor this [Low Voltage] network as well to ensure that these critical systems [control systems, relays, IEDs] remain operational".
Without reliable power, the automation system's capabilities can be severely impacted.
Alarm management is another critical component. Marggraff warns:
"If the alarm thresholds were to be defined incorrectly, an operator may be flooded with alarms reducing their ability to differentiate between actual error conditions that require their attention and false flags".
To avoid this, alarm thresholds should be carefully optimized so that important alerts stand out without overwhelming operators.
For transformers, automated cooling systems can activate when winding temperatures rise, reducing the risk of equipment trips and extending the transformer's lifespan. Sync-check relays should also be audited regularly to ensure frequency and voltage settings are accurate, preventing premature circuit breaker closures that could cause major damage.
Database integrity checks are vital for ensuring operators have accurate information. The status of ethernet switches and gateway servers should also be monitored to maintain secure data flow and remote access. Lastly, maintenance routines must verify that interlocks are functioning properly, preventing unsafe or unauthorized actions.
Ongoing monitoring and maintenance are crucial for maintaining the security and reliability achieved through these mitigation strategies.
Conclusion and Key Takeaways
Risk Assessment Essentials
When it comes to risk assessment for Substation Automation Systems (SAS), there’s a need to combine robust technical safeguards with careful human oversight. The challenge lies in implementing security measures that align with operational standards like IEC 61850 and IEC 60870 without negatively impacting system performance. A critical point to remember: operator stations inherently trust the central database. If the database’s integrity is compromised, it could lead to incorrect autonomous actions, creating confusion during critical events. This makes database validation and proper alarm threshold configuration absolutely necessary to prevent potential breaches and operational errors.
The Security Baseline approach, as discussed earlier, provides a structured way to connect identified threats with appropriate countermeasures, all while staying compliant with ISO 27001 and regulations like NIS2. Tools such as the Purdue framework and MITRE ATT&CK for Industrial Control Systems further simplify the process by breaking substations into zones - process, bay, and station levels. This zoning approach helps identify key assets and their vulnerabilities more effectively. Considering the complexity of substations, which often use more than 50 communication protocols, this method is essential for ensuring thorough protection.
Next Steps for Professionals
To strengthen your substation automation system, here are some practical steps you can take:
- Secure your Engineering Workstation: Protect configurations for Intelligent Electronic Devices (IEDs) and Programmable Logic Controllers (PLCs).
- Verify sync-check relay settings: Ensure these are properly configured to avoid operational errors.
- Deploy redundant Gateway Servers: These help maintain remote access even during system failures.
- Monitor low-voltage networks: Keep a close watch on the networks powering critical control systems.
With manufacturing backlogs causing transformer lead times of 12 to 24 months, it’s worth exploring alternative sourcing options. Platforms like Electrical Trader provide access to verified surplus and reconditioned components, such as circuit breakers, switchgear, and high-voltage transformers. These can serve as a stopgap solution when project schedules are tight or when rapid replacements are needed.
Lastly, ensure that all risk assessment outputs are aligned with ISO 27001 as well as national implementations of NIS2 to meet legal and regulatory requirements. As the grid evolves to meet the demands of AI data centers, renewable energy initiatives, and electric vehicle infrastructure, maintaining a strong and adaptive risk assessment process will be key to keeping up with these shifts in infrastructure needs.
FAQs
How do I define SAS zones and conduits correctly?
Getting the zones and conduits right in a Substation Automation System (SAS) is critical for maintaining cybersecurity and system reliability. The first step is to divide the system into zones based on their function and specific security requirements. Once that's done, you design conduits to manage and monitor the flow of data between these zones.
To ensure you're on the right track, refer to established standards like IEC 62443-3-2. This provides a framework for effective segmentation, helping you define each zone and conduit clearly. Properly setting this up minimizes the risk of misconfigurations and potential security vulnerabilities.
Which SAS assets should I assess first for the biggest risk?
When prioritizing maintenance or upgrades, begin with assets most likely to fail and those with the biggest potential impact. Pay close attention to critical substation components, such as protection relays, communication interfaces, and control systems. These elements are key to maintaining system reliability and ensuring safety, so addressing their risks should be a top priority.
How do I pick a target Security Level (SL0–SL4) for each zone?
To determine the appropriate Security Level (SL0–SL4) for each zone, start by evaluating the security needs and potential risks specific to that area. Zones containing critical or highly sensitive data are best suited for higher levels, like SL3 or SL4, as these provide stronger protections. On the other hand, less critical zones may only require SL0 or SL1, which are simpler and less resource-intensive.
The goal is to align the security level with your risk assessment. This ensures the chosen level effectively addresses potential threats while considering available resources and operational demands - without unnecessarily complicating the security framework.
