Designing Cybersecure Backup Power Systems
Share
Backup power systems are critical for ensuring operations during power outages in facilities like hospitals, data centers, and government sites. However, the increasing use of smart grids and interconnected devices has made these systems vulnerable to cyberattacks. To secure them, organizations must implement cybersecurity frameworks, follow secure design principles, and address risks at every level - from equipment to network infrastructure.
Key takeaways:
- Backup power systems are vital for critical infrastructure during grid failures.
- Cyber threats target remote controls, generators, and interconnected systems.
- Frameworks like NIST CSF, IEC 62443, and NERC CIP provide structured security approaches.
- Secure design includes multi-factor authentication, network isolation, and immutable backups.
- Collaboration between engineers, IT, and cybersecurity teams is essential for resilience.
Proactive measures like secure-by-design procurement, regular audits, and recovery planning are vital for protecting these systems against emerging threats.
Securing the grid: Cyber-security solutions in the age of distributed energy
sbb-itb-501186b
Cybersecurity Frameworks for Backup Power Systems
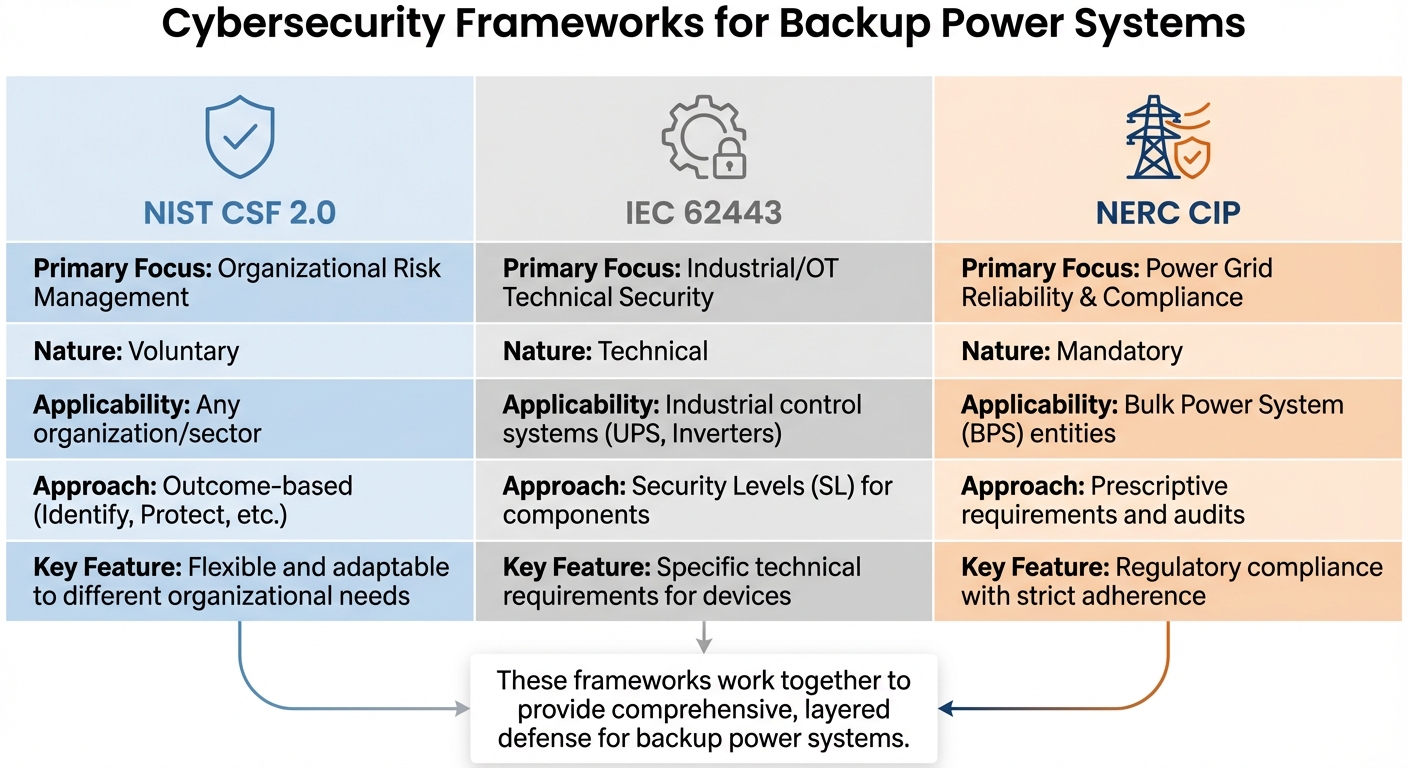
Comparison of Cybersecurity Frameworks for Backup Power Systems: NIST CSF vs IEC 62443 vs NERC CIP
In light of the cyber vulnerabilities that have been identified, using well-established frameworks is essential to secure backup power systems. Protecting these systems demands both technical know-how and adherence to reliable cybersecurity guidelines. Frameworks like the NIST Cybersecurity Framework, IEC 62443, and NERC CIP offer structured approaches to safeguard critical power infrastructure against modern cyber threats. Each framework tackles different layers of security, ranging from risk management to technical standards and regulatory compliance.
Understanding the distinctions and synergies between these frameworks is key to creating resilient and secure backup power systems. For example, the NIST framework is adaptable and broad in scope, IEC 62443 provides detailed technical requirements for industrial control systems, and NERC CIP enforces mandatory standards for power grid operators. When combined, these frameworks form a layered defense strategy, addressing various aspects of backup power security and ensuring a comprehensive approach.
Using the NIST Cybersecurity Framework
The NIST Cybersecurity Framework (CSF) 2.0 offers a flexible, risk-focused approach to managing cybersecurity concerns in backup power systems. Unlike rigid standards, the NIST CSF emphasizes outcomes, making it adaptable to different organizational risks and needs.
"The NIST IR 8286 series helps practitioners understand the critical connection between cybersecurity and Enterprise Risk Management."
Organizations can implement the framework by creating a Target Profile that defines desired security outcomes for backup power systems. This profile is built around the framework's core functions: Govern, Identify, Protect, Detect, Respond, and Recover. By comparing the Target Profile to the current state, organizations can pinpoint vulnerabilities and prioritize improvements. For backup power systems integrated with smart grid technologies, NISTIR 7628 Rev 1 provides a valuable tool for analyzing interconnectivity risks and crafting tailored security strategies.
Additionally, the NIST IR 8286 series ties cybersecurity efforts directly to Enterprise Risk Management, ensuring that backup power security is seen as a business-critical issue rather than just an IT concern. These guidelines support "secure-by-design" principles, encouraging the development of backup power components with built-in security.
IEC 62443 and NERC CIP Standards for Power Systems
While the NIST framework focuses on organizational risk management, IEC 62443 and NERC CIP address specific technical and regulatory aspects of power system security.
IEC 62443 is a set of standards aimed at Industrial Automation and Control Systems (IACS). It defines security requirements for devices like UPS units and inverters, establishing Security Levels (SL) to ensure robust protections. When choosing backup power equipment, organizations should confirm that devices comply with IEC 62443 standards, including secure communication protocols and device-level protections.
On the other hand, NERC CIP (Critical Infrastructure Protection) is a set of mandatory regulations for entities managing the North American bulk power system. These standards are not optional and require strict adherence, including regular audits. NERC CIP covers a wide range of security measures, from access controls to incident response protocols, and directly influences the design and operation of backup power systems that interact with the bulk power grid.
The table below highlights the key differences between these frameworks:
| Feature | NIST CSF 2.0 | IEC 62443 | NERC CIP |
|---|---|---|---|
| Primary Focus | Organizational Risk Management | Industrial/OT Technical Security | Power Grid Reliability & Compliance |
| Nature | Voluntary | Technical | Mandatory |
| Applicability | Any organization/sector | Industrial control systems (UPS, Inverters) | Bulk Power System (BPS) entities |
| Approach | Outcome-based (Identify, Protect, etc.) | Security Levels (SL) for components | Prescriptive requirements and audits |
Each framework plays a unique role, but together they provide a comprehensive strategy for securing backup power systems against evolving cyber risks.
How to Design Secure Backup Power Systems
Creating secure backup power systems means embedding cybersecurity into every step of the design process. This approach ensures that security isn’t an afterthought but a core part of the system architecture. To achieve this, it’s critical to involve cybersecurity experts early on, ensuring that all components - whether it’s generators, UPS units, or other elements - meet stringent security requirements.
Secure-by-Design Principles for Power Components
The secure-by-design approach focuses on implementing strong authentication and access controls. For example, instead of relying on a single shared password, a generator's control interface should require multi-factor authentication to limit access to authorized personnel only.
Another key element is ensuring data integrity to prevent tampering during command transmissions. As highlighted by NIST SP 1800-32:
"Any attack that can deny, disrupt, or tamper with DER communications could prevent a utility from performing necessary control actions and could diminish grid resiliency".
To counter such threats, systems should include continuous behavioral monitoring and immutable command registers. These measures help create a tamper-proof audit trail of all interactions between operators and power resources. Additionally, deploying OT-specific monitoring tools and centralizing logs in the cloud can enhance real-time threat detection.
Finally, network segmentation and redundancy are essential to complement these security measures.
Network Segmentation and Redundancy for Power Systems
Securing individual components is only part of the equation - network strategies play a crucial role in protecting backup power systems. Network segmentation ensures that power management systems are isolated from IT networks. For instance, telecommunications equipment monitoring generators, batteries, and UPS units should operate behind firewalls or within virtual private networks, rather than being directly exposed to the internet.
Redundant communication channels are equally important. For microgrids, technologies like LTE can provide isolated communication pathways, ensuring control remains intact even if one channel fails. Wireless broadband technologies, paired with distributed ledger systems, can also maintain an unalterable audit trail of data exchanges. Tools such as the CISA Ten Steps of Resilient Power and the Resilient Power Assessment Worksheet are invaluable for identifying and addressing vulnerabilities in network isolation and redundancy.
Choosing UPS and Inverters with Security Features
When selecting UPS units and inverters, prioritize models with strong cybersecurity features. This is particularly important given warnings from CISA and the Department of Energy about threat actors:
"gaining access to a variety of internet-connected uninterruptible power supply (UPS) devices, often through unchanged default usernames and passwords".
Devices should enforce password changes during initial setup and avoid hardcoded or universal default credentials. Secure connectivity is another critical factor. Many modern UPS systems include IoT capabilities for power monitoring and maintenance, which can introduce vulnerabilities. As noted by CISA and the Department of Energy:
"UPSs are routinely attached to networks for power monitoring, routine maintenance, and/or convenience".
To mitigate these risks, ensure that devices support secure communication protocols and can operate effectively within isolated network segments. Access control features should allow for granular user permissions, reflecting the diverse roles involved - IT teams, building operations staff, industrial maintenance workers, and third-party monitoring services. Before deployment, evaluate products for secure manufacturing processes and eliminate any public internet exposure. Always involve cybersecurity experts during procurement to integrate security considerations from the start.
Reducing Cybersecurity Risks in Backup Power Systems
Cybersecurity risks in backup power systems go beyond just the physical equipment - they extend into telecommunications and IT systems that manage power infrastructure. These risks can include digital threats, physical security vulnerabilities, and even electromagnetic risks that could disrupt the entire system. Addressing these issues requires a team effort, bringing together chief engineers, power managers, IT experts, and cybersecurity specialists. This collaboration, from procurement through daily operations, helps create a solid foundation for recovery strategies.
Immutable Backups and System Recovery Plans
When it comes to securing systems, planning for recovery is just as important as preventing attacks. Recovery strategies should safeguard not only backup generators but also critical elements like control systems, configuration data, and logs. One of the best tools for this is immutable backups - backups that can’t be changed or deleted. These serve as a cornerstone for system recovery.
The Cybersecurity and Infrastructure Security Agency (CISA) provides the Ten Steps of Resilient Power, a structured guide for creating recovery procedures tailored to critical power systems. This framework emphasizes integrating continuity planning and emergency preparedness into the lifecycle of power components. Tools like the Resilient Power Assessment Worksheet can help identify system vulnerabilities before they become threats.
Collaboration is key here. Chief engineers and IT teams must work together, both during normal operations and in crisis scenarios. When procuring power equipment, security requirements should be baked into the process alongside technical specifications. This ensures recovery plans align with the actual capabilities of the installed systems.
Planning for Ransomware and Major Cyber Attacks
Ransomware attacks can cripple power systems by disabling monitoring tools and blocking access to controls. To counteract these threats, security must be integrated into every step - from equipment procurement to contractor management during maintenance. Procurement teams should prioritize vendors who follow Secure-by-Design principles, such as eliminating default credentials, supporting secure communication protocols, and providing timely updates.
External contractors also play a role in maintaining security. By involving them in continuity planning, organizations can ensure their maintenance practices align with security standards. Similarly, IT and telecommunications staff should be part of the conversation when specifying power solutions, as their input helps guard against both cyber and electromagnetic threats.
Regular training sessions on resilient power guidelines can help operations and maintenance staff avoid common mistakes, such as configuration errors or leaving security gaps. Tools like the Resilient Power Assessment Worksheet provide a structured way to document and address vulnerabilities systematically.
In addition to prevention, detailed record-keeping is critical for rapid recovery after an attack.
Asset Tracking and Configuration Management
Accurate asset tracking is a cornerstone of cybersecurity. Knowing exactly what equipment you have, where it’s located, and how it’s configured helps detect unauthorized changes or rogue devices in the network. Effective configuration management involves documenting every aspect of your systems - UPS units, generators, inverters, and control systems. This includes detailed records of equipment setups, access permissions, and communication pathways.
Every configuration change should be logged, and asset tracking should be integrated into continuity planning. This ensures that recovery teams have immediate access to up-to-date system inventories and configuration baselines when responding to a cyber incident. Cross-functional oversight is essential, especially for high-risk assets, to ensure they receive the attention they need during emergencies.
Conclusion
Ensuring reliable backup power systems for critical infrastructure is no longer a choice - it's a necessity. With nation-state attacks, ransomware, and outdated infrastructure becoming more prevalent, the risks are escalating dramatically. In 2022 alone, cyberattacks targeting critical infrastructure surged by 140%, and cybercrime damages are expected to surpass $6 trillion annually. The urgency to act has never been greater.
To address these threats, organizations must rethink their strategies. Cybersecurity needs to be integrated from the very beginning. Using frameworks like NIST CSF 2.0 and IEC 62443, along with Secure-by-Design procurement and strict network segmentation, helps create a layered defense capable of resisting even sophisticated attacks.
On top of these technical measures, having cross-functional teams in place ensures accountability and swift decision-making during crises. Regular testing, clear leadership structures, and robust recovery plans are key to minimizing downtime. Accurate asset tracking, meticulous configuration management, and immutable backups provide the solid foundation organizations need to respond effectively to incidents.
"Security failures don't always start with attackers, sometimes they start with missing truth".
The move from voluntary guidelines to mandatory compliance, as seen with the EU NIS2 Directive's 24-hour incident notification requirement, underscores the increasing importance of these systems.
True resilience means more than just surviving an attack - it’s about adapting and recovering quickly. By prioritizing cybersecurity in the design phase of backup power systems, organizations can better safeguard the critical infrastructure that underpins our modern way of life.
FAQs
Which cybersecurity framework should I start with for backup power systems?
The NIST Cybersecurity Framework (CSF) serves as an excellent foundation for protecting backup power systems. It provides detailed guidance to help manage cybersecurity risks across critical infrastructure. Starting with CSF 2.0 is a smart move - it includes templates and quick-start guides designed to simplify the process of integrating layered security into your resilience planning. This ensures that cybersecurity becomes an essential part of your backup power system design.
How do I isolate backup power controls from my IT network safely?
To keep backup power controls securely isolated from your IT network, network segregation is key. This involves setting up dedicated control network segments with both physical and logical separation. Make sure only authorized personnel have access by enforcing strict access controls.
Adding layers of protection, like continuous monitoring and cutting off non-essential communications, strengthens your defenses. These measures are essential for minimizing vulnerabilities and blocking unauthorized access effectively.
What should I require in UPS and inverter procurement to avoid cyber risks?
To reduce cyber risks when purchasing UPS and inverters, consider these key measures:
- Supply Chain Security: Carefully evaluate vendors for potential vulnerabilities and insist on robust risk management protocols.
- Firmware Integrity: Confirm that firmware updates are secure, verified, and protected against unauthorized tampering or control.
- Access Controls: Implement strong, unique credentials, enable multifactor authentication, and limit internet access to essential needs.
By following these steps, you can help ensure your systems remain secure and reliable throughout their lifecycle.
Related Blog Posts
- IEC 62040-1 for Backup Power Systems
- Digital Twin Cybersecurity: Best Practices 2025
- How Cybersecurity Protects Medium Voltage Motor Controls
- Top IEEE 446-1995 Recommendations for Standby Power