
How Cybersecurity Protects Medium Voltage Motor Controls
Share
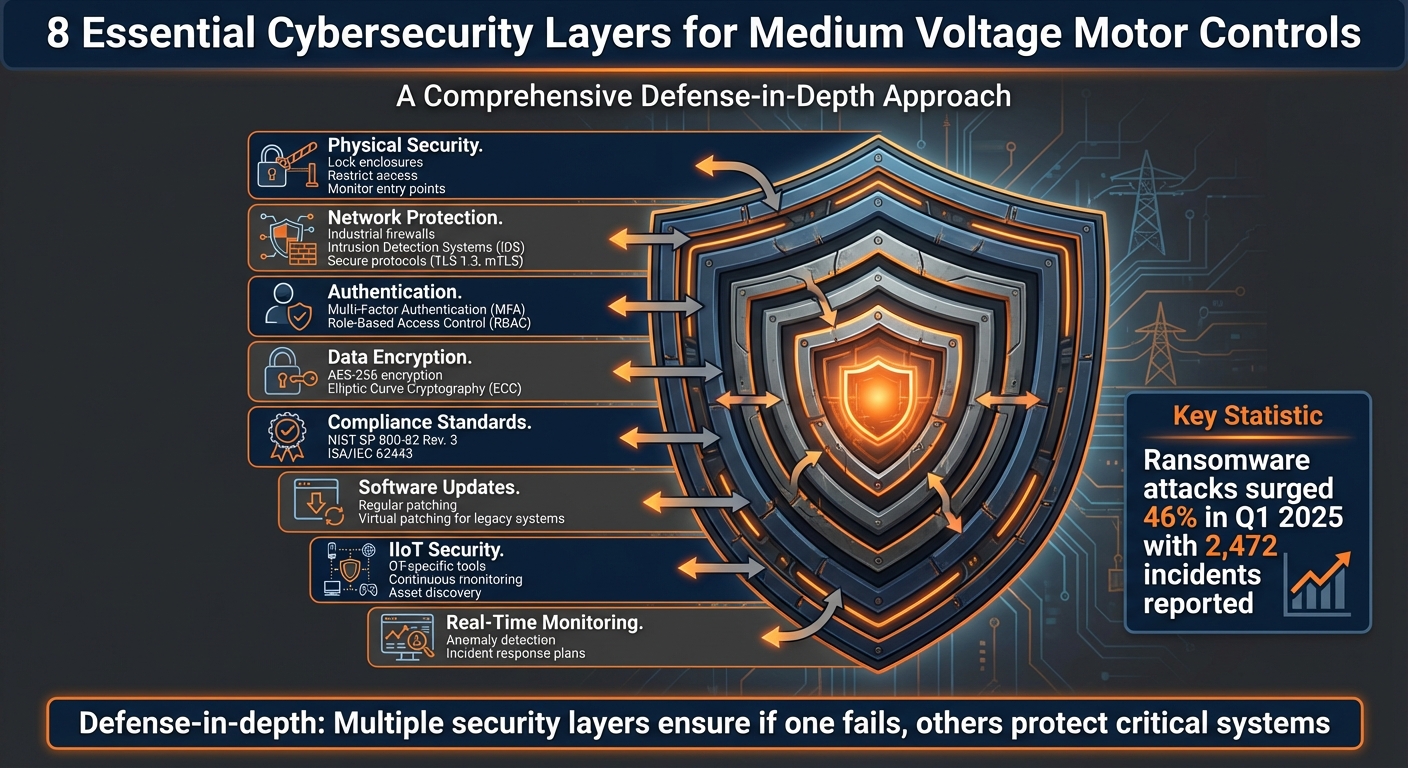
Medium voltage motor controls are vital for managing industrial operations, but they face increasing cyber threats due to outdated designs and IT-OT integration. Here's how cybersecurity measures can protect these systems:
- Physical Security: Lock enclosures, restrict access, and monitor entry points to prevent tampering.
- Network Protections: Use industrial firewalls, intrusion detection systems (IDS), and secure protocols like TLS 1.3 or mTLS.
- Authentication: Implement multi-factor authentication (MFA) and role-based access control (RBAC) for system access.
- Encryption: Secure data with AES-256 or Elliptic Curve Cryptography (ECC) to protect sensitive information.
- Compliance: Follow standards like NIST SP 800-82 Rev. 3 and ISA/IEC 62443 to address industrial cybersecurity needs.
- Software Updates: Regularly patch systems or use virtual patching for legacy equipment to mitigate vulnerabilities.
- IIoT Risks: Secure Industrial Internet of Things (IIoT) devices with OT-specific tools and continuous monitoring.
- Layered Defense: Combine physical, network, and software protections to create multiple security layers.
Cyber threats like ransomware and advanced malware are escalating, highlighting the need for a proactive, layered approach to safeguard these critical systems. By addressing vulnerabilities and following established guidelines, industries can reduce risks while maintaining system performance and reliability.
8-Layer Cybersecurity Defense Strategy for Medium Voltage Motor Controls
Electric Substation & Cyber Security | IEC 61850 Communication Networks | Key Cybersecurity Standard
Core Cybersecurity Methods for Medium Voltage Motor Controls
Securing medium voltage motor controls requires a blend of strategies that address both digital and physical risks. The NIST SP 800-82 Rev. 3 framework serves as the current benchmark for safeguarding these systems. Below is an overview of key methods used to protect these critical infrastructures.
Physical Access Controls
Physical security is the first line of defense. Protect components like PLCs, control panels, and DCS units with locked enclosures, restricted access policies, and entry-point monitoring to prevent tampering. Identifying all potential physical access points, including PLC ports and control panels, is crucial. These measures must be integrated into a broader risk management plan while ensuring they do not interfere with the high-reliability demands of medium voltage equipment.
Network Protection Methods
Securing network communications is vital, and tools like industrial firewalls, intrusion detection systems (IDS), and VPNs play a key role. These technologies must be implemented carefully to avoid compromising safety-critical operations. As NIST SP 800-82 Rev. 3 explains:
"This document provides guidance on how to secure Industrial Control Systems (ICS)... while addressing their unique performance, reliability, and safety requirements."
The framework also emphasizes identifying vulnerabilities in common system architectures and applying countermeasures to safeguard SCADA, PLC, and DCS communications. These steps should enhance security without causing latency or operational issues. Adding robust authentication protocols further strengthens network defenses.
User Authentication and Access Control
Multi-factor authentication (MFA) and role-based access control (RBAC) are essential for restricting system access to authorized personnel. These methods must align with the specific communication patterns of SCADA and DCS architectures. Authentication gateways and access control lists should be tailored to the system's layout to maintain operational efficiency. By acting as a final layer of defense, these measures help protect against both internal and external threats, forming a critical part of a layered security approach.
Technical Protections and Industry Standards
Data Encryption Methods
Encryption is the process of converting data into a secure, unreadable format. For medium voltage motor controls, AES-256 (Advanced Encryption Standard with 256-bit keys) stands out as one of the most secure symmetric encryption methods available. It’s trusted by the U.S. government to safeguard classified information. This approach is ideal for managing large amounts of operational data without slowing down real-time control systems.
Another option gaining traction is Elliptic Curve Cryptography (ECC). Its efficiency is impressive - a 256-bit ECC key provides the same level of security as a 3,072-bit RSA key but with faster performance, making it a preferred choice in industrial applications.
To further bolster security, implement Transport Layer Security (TLS) 1.3 and Mutual TLS (mTLS). These protocols ensure both endpoints are authenticated before any data exchange occurs. During remote access sessions, always encrypt data using VPNs or secure industrial protocols. Additionally, keep encryption keys stored in a centralized, secure location separate from the systems they protect.
Strong encryption practices are the backbone of meeting stringent cybersecurity standards.
Industry Standards Compliance
Encryption alone isn’t enough - adhering to established cybersecurity standards is equally important. The ISA/IEC 62443 series is a widely recognized framework for securing Industrial Automation and Control Systems (IACS). This standard addresses the unique challenges of operational technology, defining five Security Levels (SL 0 to SL 4) based on the sophistication of potential threats. Notably, in 2018, the United Nations Economic Commission for Europe incorporated ISA/IEC 62443 into its Common Regulatory Framework on Cybersecurity.
These standards are already in use by NATO, which applies them to assess cyber risks in critical infrastructure, such as the Central Europe pipeline system. As quantum computing evolves, it introduces new security challenges. To prepare, organizations must adopt Post-Quantum Cryptography (PQC) measures. In December 2025, the U.S. Department of War mandated that all Pentagon components transition to quantum-resistant technologies to counter these emerging threats.
Software Updates and Vulnerability Management
Maintaining secure systems goes beyond encryption and compliance - it also requires regular software updates and vulnerability management. Many legacy motor control systems run outdated software, leaving them exposed to critical vulnerabilities. A structured patch management process is essential to address these risks. This involves monitoring, testing, and deploying updates across all components.
For systems that can’t afford downtime, virtual patching offers an alternative. It provides protection without requiring a system reboot, ensuring continuous uptime - a critical need for medium voltage operations. Regular vulnerability assessments are also crucial. These evaluations help identify and prioritize risks based on the specific needs of your operational environment. Moreover, product suppliers should adhere to IEC 62443-4-1 standards throughout the development lifecycle, embedding security into motor controls from the design phase through maintenance.
sbb-itb-501186b
Cybersecurity for IIoT-Connected Motor Control Systems
IIoT Integration: Advantages and Security Risks
The Industrial Internet of Things (IIoT) connects sensors, instruments, and motor controls to cloud platforms, enabling improved efficiency and predictive maintenance. Using OT-rated routers and switches, these components communicate via industrial protocols like MODBUS and BACNET. While this connectivity enhances operations, it also broadens the potential attack surface.
In early 2025, ransomware attacks surged by 46%, with 2,472 incidents reported in the first quarter alone - already accounting for 40% of the total incidents in 2024. This sharp increase highlights the risks associated with expanding IIoT adoption in smart manufacturing. More connected devices mean more potential entry points for cyberattacks.
As Claroty noted:
"The threat is rapidly intensifying as these attacks against the enterprise network can force organizations to halt operations until remediated." - Claroty
One critical vulnerability lies in the lack of built-in security for many IIoT devices. This becomes especially problematic when contractors or vendors rely on non-enterprise-grade remote access tools. A recent example occurred in May 2025, when Nucor Steel, a major US-based steelmaker, detected unauthorized third-party access to its enterprise network. The breach disrupted production at multiple facilities and restricted access to essential operational systems. Such incidents underscore the urgent need for robust security measures.
Protecting IIoT-Enabled Motor Controls
Given these risks, securing IIoT-enabled motor controls requires tailored approaches. Generic IT tools often fall short in addressing the unique demands of operational technology (OT) environments. The updated NIST SP 800-82 Rev. 3, released in September 2023, offers the latest guidance for safeguarding these systems. It emphasizes that security measures should mitigate threats without causing delays or disruptions that could impact real-time operations.
A strong starting point is continuous asset discovery. Automated tools can provide a real-time inventory of all IIoT-connected devices, helping to identify unauthorized or "shadow" devices that might have been added without proper oversight. Replace generic remote access tools with OT-specific solutions that include advanced monitoring, logging, and auditing capabilities for third-party activities. Additionally, ensure that network equipment is compatible with proprietary OT protocols.
For devices with known vulnerabilities that cannot be patched, immediate action is essential. This could mean decommissioning or isolating outdated equipment like CCTV cameras, sensors, or older controllers that no longer receive security updates. When implementing these security measures, it’s crucial to prioritize the availability and safety-critical functions of motor controls. After all, operational reliability must remain intact even as systems are secured.
As Claroty points out:
"If a malware attack brings a critical piece of equipment offline, for example, it could create financial and reputational damage for the company, and endanger the physical safety of workers." - Claroty
Layered Defense Strategy for Medium Voltage Motor Controls
Multi-Layer Security Framework
When it comes to protecting medium voltage motor control systems, a defense-in-depth strategy is key. This approach creates multiple layers of security, ensuring that even if one layer is compromised, others remain in place to safeguard the system. The strategy integrates physical security, network isolation, and software-level protections, all designed to meet the unique needs of industrial environments where reliability and real-time performance are critical.
At the core of this strategy is network segmentation. By implementing firewalls and VLANs, operators can separate control networks - where PLCs and motor drives function - from the larger corporate IT infrastructure. This limits the potential damage or "blast radius" if a breach occurs elsewhere. Physical access controls provide an additional layer of protection, ensuring that unauthorized individuals cannot tamper with controllers or connect unauthorized devices directly to motor control panels.
The next layer focuses on securing the control devices themselves. PLCs and Distributed Control Systems (DCS) should run only essential functions, with all non-critical services disabled. However, these measures must be applied carefully to avoid interfering with the real-time communication necessary for motor protection. By layering defenses in this way, you create a robust system that maintains operational reliability while allowing for vigilant monitoring and threat detection.
Real-Time Monitoring and Response Plans
Adding to these security layers, continuous monitoring plays a vital role in detecting and addressing threats before they escalate. Monitoring tools analyze network traffic and system behavior in real time, looking for anomalies that might indicate unauthorized access or malware activity. In industrial settings, even a small delay in identifying threats can lead to serious consequences.
Incident response plans tailored to industrial control systems are essential. Standard IT response procedures often overlook the specific configurations of PLCs and SCADA systems used in motor control operations. These plans should prioritize safety and system stability, outlining clear steps to isolate affected systems without disrupting broader operations. Regularly testing these response plans ensures teams are prepared to act quickly and effectively during a cyber event, reducing downtime and protecting both equipment and personnel.
Conclusion: Building Secure Medium Voltage Motor Control Systems
Protecting medium voltage motor controls requires a multi-faceted approach tailored to the challenges of industrial environments. This guide has explored key defenses like physical access controls, network segmentation, encryption, authentication, and continuous monitoring. Together, these layers create a robust shield that not only safeguards critical systems but also upholds the performance, reliability, and safety essential for industrial operations.
The risks are undeniable. As CISA warns, "OT devices lack authentication and authorization methods that are resistant to modern threats and are quickly found by searching for open ports on public IP ranges". This makes swift action critical. Start by examining all public-facing assets and disconnecting OT systems from the public internet. Implement strong manufacturer password policies and ensure all remote access uses phishing-resistant MFA. These steps significantly reduce your system's exposure to threats.
For long-term protection, adopt a security-first mindset. Align your strategy with established frameworks like NIST SP 800-82 Rev. 3, which replaced Rev. 2 in 2023, as covered earlier in this guide. Regularly update your asset inventory, audit configuration settings, and practice manual operation capabilities to prepare for potential disruptions. Collaborate with system integrators and manufacturers to identify and address misconfigurations before they escalate into vulnerabilities.
Security isn't a one-time effort - it’s a continuous process. CISA underscores this point: "The capability for organizations to revert to manual controls to quickly restore operations is vital in the immediate aftermath of an incident". Regularly test your incident response plans, apply software patches promptly, and maintain open communication with third-party service providers. These measures reinforce the proactive, layered security approach outlined in this guide. When investing in new equipment, prioritize components that are Secure by Design to ensure security is integrated from the ground up.
FAQs
What are the best ways to protect medium voltage motor controls from cyber threats?
Protecting medium voltage motor controls from cyber threats calls for a layered security strategy. Start with strong access controls: change default passwords immediately, limit physical access to authorized personnel, and enable two-factor authentication for remote connections. Keeping firmware and software up to date is also crucial for addressing vulnerabilities. To further secure your systems, implement network segmentation, which restricts unauthorized access to critical areas.
Other effective steps include using application whitelisting to prevent malware from running, conducting regular risk assessments to identify potential weak points, and training your team to detect and respond to cyber threats. Adopting a defense-in-depth approach - where multiple security measures work together - adds extra layers of protection and boosts system resilience. By staying diligent with these practices, you can better safeguard your motor control systems against the ever-changing landscape of cyber threats.
How does network segmentation improve the security of medium voltage motor control systems?
Network segmentation strengthens the security of medium voltage motor control systems by isolating critical control networks from less secure areas of the enterprise network and external connections. This separation helps limit the spread of cyberattacks, effectively reducing the potential attack surface.
By breaking the network into smaller, secure zones, organizations can better contain breaches and block unauthorized access to essential systems. This layered defense ensures that even if one part of the network is compromised, the core motor control systems remain shielded. In today’s interconnected world, network segmentation serves as a key strategy for protecting critical infrastructure.
Why is it essential to combine physical and digital security for motor control systems?
Combining physical and digital security is essential when it comes to safeguarding medium voltage motor control systems. Physical security works as the first line of defense, blocking unauthorized access to hardware and preventing risks like tampering, sabotage, or even cyber intrusions.
By pairing these two layers of protection, you create a more secure system that's better equipped to handle both physical and digital threats. This dual approach not only keeps critical infrastructure safe but also helps minimize the chances of expensive downtime or potential damage.
