How Cyberattacks Target Substation Supply Chains
Share
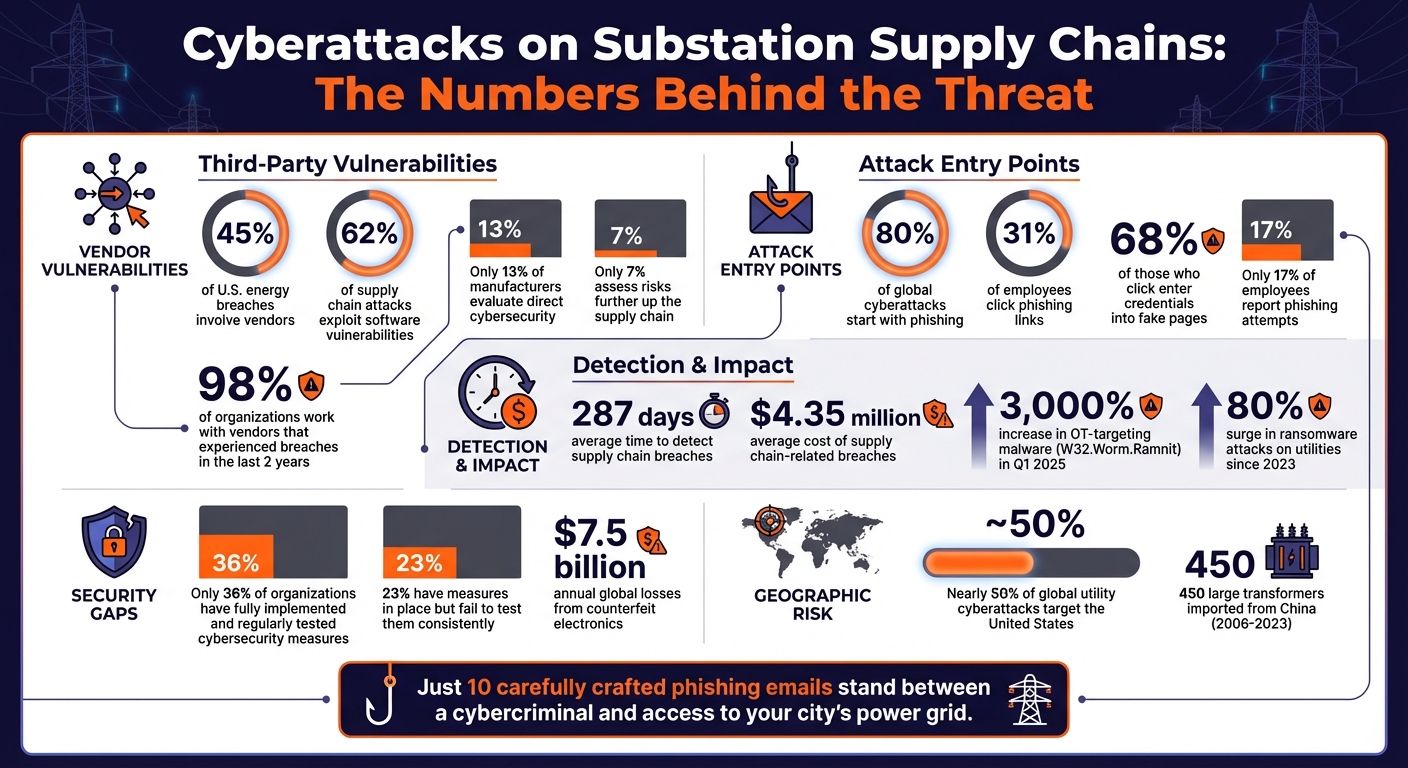
Electrical substations face growing cyber threats, with supply chain vulnerabilities being a key target. From outdated systems to unsecure vendor software, attackers exploit these weak points to disrupt power grids. The January 2026 blackout in Caracas, Venezuela, highlights the real-world consequences of such attacks. Here's what you need to know:
- Third-party risks: 45% of U.S. energy breaches involve vendors, with 62% linked to software flaws.
- Outdated equipment: Legacy devices with old firmware and insecure protocols are easy targets.
- Remote access issues: Poorly secured VPNs and cloud portals expand the attack surface.
- Common attack methods: Phishing, compromised updates, and man-in-the-middle (MitM) attacks are frequently used.
Key solutions include:
- Conducting thorough supplier risk assessments.
- Implementing network segmentation and continuous monitoring.
- Regularly patching and securely configuring systems.
- Verifying equipment sourcing to avoid counterfeit components.
Cybersecurity in supply chains is no longer optional - it’s a priority to protect critical infrastructure.
Substation Supply Chain Cyber Threats: Key Statistics and Vulnerabilities
Get to know the 7 cybersecurity building blocks for a secure substation
sbb-itb-501186b
Vulnerabilities in Substation Supply Chains
Substation supply chains are riddled with weak points that attackers frequently exploit. These vulnerabilities arise from reliance on third-party suppliers, outdated infrastructure, and the growing interconnectivity of systems that were once isolated. Identifying these gaps is a critical step in protecting vital power infrastructure. Let’s break down the key areas of concern: supplier relationships, aging systems, and connectivity challenges.
Third-Party Supplier Risks
Third-party suppliers are one of the biggest weak links in substation supply chains. Attackers often target smaller vendors, knowing they are less secure, to infiltrate larger utility companies. Statistics paint a concerning picture: 98% of organizations work with vendors that have experienced breaches in the last two years, and 62% of supply chain attacks exploit software vulnerabilities.
The lack of oversight adds to the problem. Only 13% of manufacturers evaluate the cybersecurity measures of their direct suppliers, and a mere 7% assess risks further up the chain. This oversight gap allows vulnerabilities in embedded software - such as those in controllers, sensors, and grid management devices - to spread unchecked. Once compromised, these devices can act as "quiet sensors", feeding attackers critical metadata to identify the best points of disruption.
"Cyber criminals don't always target you - they target who you trust." – PureCyber
One common tactic is the use of trojanized updates, where attackers inject malicious code into legitimate software patches. This approach bypasses traditional defenses, delivering malware straight into operational technology (OT) systems. The consequences are costly: supply chain-related breaches average $4.35 million in damages and take an alarming 287 days to detect. During this time, attackers can establish persistent access and map critical systems for future attacks.
Legacy Systems and Unpatched Devices
Aging substation equipment is another major vulnerability. Devices like Remote Terminal Units (RTUs), older protection relays, and SCADA systems often run on outdated firmware and insecure protocols such as Modbus and DNP3, which lack modern authentication features. Many legacy devices still rely on hard-coded diagnostic accounts or backdoor Telnet access, making them easy targets for attackers who can inject malicious firmware or erase configurations. Physical access only worsens the situation, as internal hardware jumpers on older relays can bypass software-based security entirely.
The challenge of keeping systems updated is growing. According to Joe Saunders, CEO of RunSafe Security, "AI now enables attackers to produce exploits faster than operators can patch them". This means that known vulnerabilities in unpatched devices are being weaponized before utility operators can respond. Compounding the issue, many older systems cannot support modern security measures like multi-factor authentication (MFA) or encrypted communication. Despite this, only 36% of organizations have fully implemented and regularly tested cybersecurity measures, while 23% have measures in place but fail to test them consistently. These gaps leave critical infrastructure exposed to persistent threats.
But the risks don't stop with outdated hardware. Increasing digital connectivity is opening up new avenues for attackers.
Remote Access and Connectivity Weaknesses
The blending of IT and OT systems has significantly expanded the attack surface for substations. Remote access points provided by vendors, VPNs, and Remote Desktop Protocol (RDP) sessions are now common targets. The shift to cloud-based management and third-party portals - accelerated during the COVID-19 pandemic - has further multiplied potential vulnerabilities.
Attackers exploit these openings using tools like Shodan, an internet-scanning service that identifies industrial control system devices directly connected to the internet. Jim LaBonty, Retired Head of Global Automation Engineering at Pfizer, Inc., cautions:
"Directly exposing these systems to the internet exposes companies to undue risk; attackers can use internet-scanning services such as Shodan to enumerate devices directly communicating online".
Weak security practices, such as the absence of multi-factor authentication and the use of shared credentials by third-party administrators, make credential-based attacks even easier. Once inside, attackers can move laterally across networks, taking advantage of poor segmentation between business systems and critical substation controls. Additionally, smart meter remote management networks and third-party cloud portals provide attackers with further entry points to map the grid and identify weak spots for large-scale disruptions. These connectivity issues turn essential operational tools into dangerous vulnerabilities, threatening the stability of entire power distribution networks.
Common Cyberattack Methods on Substation Supply Chains
Attackers often take advantage of supply chain vulnerabilities using highly targeted methods. Understanding these approaches is crucial for preventing breaches. Among the most common tactics are phishing campaigns, compromised updates, and man-in-the-middle (MitM) attacks. Each method plays on the trust that underpins supply chain relationships.
Phishing and Social Engineering
Phishing remains one of the most common ways attackers infiltrate substations. In fact, nearly 80% of global cyberattacks start with a phishing email. By leveraging publicly available information like LinkedIn profiles, company directories, and public records, attackers craft spear-phishing emails tailored to engineers and procurement staff. These emails often appear to come from trusted colleagues or vendors, making them highly convincing.
The numbers speak for themselves: about 31% of employees click on phishing links, and of those, 68% proceed to enter their credentials into fake login pages. Alarmingly, only 17% of employees report these phishing attempts. The rise of Phishing-as-a-Service (PhaaS) platforms has made it easier than ever for attackers to launch these campaigns. These platforms offer ready-made spoofed websites and fake login forms, lowering the technical barrier for cybercriminals.
PhishCloud emphasizes the severity of this threat:
"Just ten carefully crafted phishing emails stand between a cybercriminal and access to your city's power grid. Not thousands. Not hundreds. Ten."
This strategy exploits trust within supply chains and highlights the need for vigilance and employee training to combat these threats.
Malware Through Compromised Hardware or Software Updates
Once attackers gain initial access, they often exploit trusted system updates to spread malware. Substations rely heavily on software and hardware updates from known vendors, and attackers use this trust to their advantage. On average, it takes 287 days to detect such breaches, giving attackers plenty of time to establish a foothold.
One method involves tampering with software updates. For example, during the Dragonfly campaign, attackers replaced legitimate software installers on vendor websites with versions containing the Backdoor.Oldrea Remote Access Trojan (RAT). Similarly, the SolarWinds breach in December 2020 demonstrated the scale of such attacks. Nation-state actors inserted the "Sunburst" backdoor into Orion software updates, affecting 18,000 customers, including U.S. government agencies and Fortune 500 companies.
Hardware-based threats are also on the rise. "Evil PLC" attacks weaponize programmable logic controllers to compromise engineering workstations during regular maintenance. Counterfeit equipment poses another danger. In one case, fake Yokogawa differential pressure transmitters - nearly indistinguishable from the real thing - were found to lack proper safety standards and potentially included cyber vulnerabilities. Meanwhile, malware like the W32.Worm.Ramnit trojan, which targets operational technology (OT) systems, saw a staggering 3,000% increase in activity during Q1 2025.
These examples highlight the importance of rigorous supplier assessments and secure update protocols.
Man-in-the-Middle (MitM) Attacks
MitM attacks take advantage of compromised communication channels to intercept and manipulate data. These attacks target the growing connectivity between substations, third-party cloud portals, remote management systems, and vendor networks.
By positioning themselves between two communicating parties, attackers can steal credentials, map grid infrastructure, and identify critical points for disruption - all without raising alarms. Joe Saunders, CEO of RunSafe Security, explains:
"Gaining access to devices allows adversaries to answer questions like: What are the peak demand times? Which distributed energy resources (DERs) are most relied upon?"
This information allows attackers to plan large-scale disruptions during moments of peak vulnerability.
MitM attacks are particularly hard to detect because they exploit the normal flow of data. Attackers can alter firmware updates in transit, redirect communications to malicious servers, or simply observe traffic to map substation operations. The increasing overlap of IT and OT systems has only made these attacks easier, as operational data now travels across networks that were not originally designed with strong security measures. These risks underscore the need for strategies like network segmentation and continuous monitoring to protect critical systems effectively.
Solutions to Prevent Substation Supply Chain Cyberattacks
Preventing cyberattacks on substation supply chains demands a proactive approach that combines strong vendor practices, secure network design, and consistent operational vigilance. By focusing on prevention, detection, and swift responses, utilities can significantly reduce their exposure to threats.
Supplier Risk Assessments
Choosing the right vendors is a critical first step in securing the supply chain. Third-party vulnerabilities often serve as entry points for attackers, so it's essential to work only with suppliers that demonstrate strong security protocols.
Vendors should adhere to established security frameworks like NIST's Cyber Supply Chain Risk Management (C-SCRM) or the Secure Software Development Framework (SSDF). Contracts should include mandatory breach notification clauses - ideally requiring disclosure within 24–48 hours of an incident - and demand certifications such as SOC 2 or ISO 27001.
Maintaining a Software Bill of Materials (SBOM) is also crucial. This inventory lists all software components and dependencies, enabling the use of Software Composition Analysis (SCA) tools to quickly identify vulnerabilities when new threats emerge. Considering that 62% of supply chain attacks exploit software vulnerabilities, knowing what's in your environment can make the difference between a quick fix and a prolonged crisis. Additionally, verifying the integrity of physical components during procurement helps mitigate risks like malicious firmware or counterfeit parts.
This thorough, risk-based approach provides a solid foundation for minimizing lateral movement, which brings us to the importance of network segmentation.
Network Segmentation and Continuous Monitoring
Segmenting networks is a powerful way to limit an attacker’s ability to move through a system. Modern digital substations often use a three-layer architecture: the Process Bus for time-critical protection, the Station Bus for supervisory control, and Engineering Access for privileged maintenance. The Process Bus, which handles sensitive operations like issuing trip commands within 4–20 milliseconds, should operate on a dedicated network segment. Redundancy protocols such as Parallel Redundancy Protocol (PRP) and High-availability Seamless Redundancy (HSR) ensure that critical communications remain uninterrupted.
To secure communication between IT and operational technology (OT) systems, implement an Industrial Demilitarized Zone (IDMZ) fortified with jump hosts and VPNs requiring multi-factor authentication (MFA). Continuous monitoring is equally essential. Passive traffic sniffing and protocol-specific probes (e.g., IEC 61850 MMS, DNP3, and Modbus) can detect anomalies without disrupting sensitive systems. Logic-level monitoring - tracking indicators like BADPASS for failed logins or SETCHG for unauthorized changes - can also catch tampering in real time.
Physical and cyber security should work hand-in-hand. For example, integrating Electronic Access Control Systems (EACS) with SCADA can trigger alerts if cabinet doors are opened without an authorized user logged onsite. A noteworthy example is the 2018 Walney Extension substation in the UK, which used a robust security system combining mesh fences and a Gallagher Monitored Pulse Fence to detect unauthorized access.
"Securing protection relays is no longer just a best practice; it's absolutely essential for ensuring the resilience of both transmission and distribution power grids." – Mandiant Services
Beyond segmentation and monitoring, keeping systems securely configured and up-to-date is equally important.
Secure Configuration and Regular Patching
One of the simplest yet most effective measures is changing default credentials on devices like relays and switches immediately after installation. Adopting a zero-trust model, which limits access to specific network segments and requires ongoing re-authentication, adds another layer of security. In highly sensitive environments, consider implementing "no-alone zones", where two authorized individuals must be present for critical operations.
Regular firmware updates are a must. With the average time to detect a supply chain compromise at 287 days, timely patching can prevent vulnerabilities from being exploited. Use code signing and digital signatures to verify the integrity of updates, and complement these measures with behavioral monitoring to detect unusual activity.
A hybrid approach to patch management often works best. Automated patching is suitable for IT systems and less critical OT components, while manual updates - tested thoroughly - are better for time-sensitive equipment like protection relays. In some cases, air-gapping critical systems can provide extra isolation, though this method may introduce operational challenges.
Monitoring third-party access is another key defense. Behavioral analytics can flag unusual activity, which is especially important given that ransomware attacks on utilities have surged by 80% since 2023, and nearly half of all global cyberattacks on utilities target the United States.
"A single weak link in the supply chain can compromise the entire system, leading to data loss, which is hard to contain." – Fortinet
Consolidating security tools into unified platforms can also make a big difference. Fragmented systems often lead to complexity and alarm fatigue, while a single platform simplifies operations and reduces the workload on security teams.
"Fragmented point solutions increase complexity and alarm fatigue. Consolidation into a single platform reduces operator workload." – Gallagher Content Team
Verified Equipment Sourcing for Cybersecurity
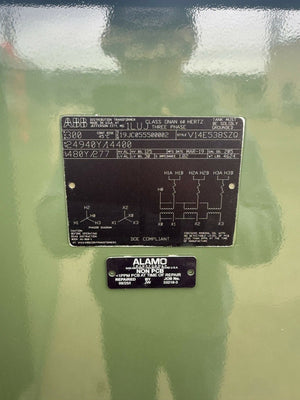
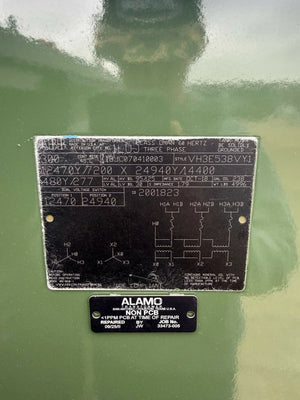
Securing the supply chain starts with ensuring the origins of equipment are verified. In substations, counterfeit electronics pose a dual threat: they compromise reliability and create vulnerabilities for cyberattacks. These risks contribute to global losses exceeding $7.5 billion annually. Even one compromised transformer or circuit breaker can lead to catastrophic failures or provide attackers with access to your substation network.
The danger isn't limited to outright counterfeits. "Remarked" components (lower-grade parts relabeled as high-grade) and "harvested" parts (used components repackaged as new) also present serious risks. For instance, in 2022, a food processing plant in Ohio replaced a failed variable frequency drive with a unit purchased from an unverified online source. The replacement, which turned out to be a counterfeit IGBT module, failed within just eleven days, causing extensive damage to other components. The repair bill ended up being four times the cost of a genuine unit.
Between 2006 and 2023, the U.S. imported nearly 450 large transformers (over 10,000 kVA) from China. This raises concerns about vulnerabilities in unmonitored hardware. Hardware backdoors in transformers and inverters could allow remote sabotage or data breaches. These examples make it clear: verifying equipment sources is not just about quality control - it’s a critical cybersecurity measure.
Benefits of Trusted Marketplaces
To address these risks, trusted marketplaces offer documented supply chain traceability, enabling buyers to track components back to their original manufacturers. This transparency is crucial, especially since 45% of U.S. energy breaches stem from third-party vendors. Reputable distributors conduct thorough inspections, including visual checks for irregular markings and electrical tests to confirm that switching characteristics match datasheets.
Platforms like Electrical Trader (https://electricaltrader.com) specialize in providing access to breakers, transformers, and power distribution equipment with verified sourcing documentation. By partnering with marketplaces that carefully vet suppliers and follow strict storage and handling protocols, utilities can sidestep the reliability issues often associated with "gray market" components.
"When cheap products are of unknown quality and cannot be traced to their point of origin, the risk associated with them is unacceptable. Power generators have too much to lose to allow questionable electrical products in a plant's infrastructure." – Tom Grace, Anti-Counterfeiting and Brand Protection Manager, Eaton
To ensure authenticity, request traceability documents like invoices or lot certificates, and be wary of prices that seem significantly below market averages. Before installing high-value components, perform layered inspections, including visual checks (for signs like blurry markings or sanding residue) and electrical testing. If you suspect a component is counterfeit, quarantine it and report it immediately to prevent it from re-entering the supply chain. This multi-step verification complements broader supplier risk assessments and strengthens overall network security.
Verified sourcing does more than protect against counterfeits - it also helps prevent hardware-based cyberattacks. A notable example occurred in March 2023, when Duke Energy disconnected energy storage batteries made by the Chinese company CATL at Marine Corps Base Camp Lejeune. U.S. lawmakers raised concerns that these batteries and their inverters posed a security risk to the electricity grid. This case highlights an essential truth: a secure supply chain isn’t just a technical safeguard - it’s a strategic advantage.
Conclusion
Substation supply chains are increasingly under siege from cyber threats, which have surged due to vulnerabilities in vendor systems, outdated technologies, unpatched devices, and the growing convergence of IT and OT systems. These challenges highlight the pressing need for a new approach to cybersecurity.
To tackle these risks, cybersecurity must become an integral part of enterprise risk management. As Erin Illman, Partner and Chair of the Energy Cybersecurity and Privacy Team at Bradley Arant Boult Cummings, puts it:
"Cybersecurity should be integrated into enterprise risk management and treated as a core business continuity issue".
This perspective requires moving beyond simple compliance measures. Organizations need to adopt strategies like thorough supplier risk assessments, network segmentation, real-time monitoring, and strict patch management protocols.
Another critical step is ensuring verified equipment sourcing to combat supply chain attacks, which have not only become more frequent but also harder to detect. Ignoring the origins of substation components can leave systems vulnerable to counterfeit or compromised hardware. Trusted platforms like Electrical Trader (https://electricaltrader.com) offer a way to source components from validated suppliers, reducing the risk of hidden vulnerabilities. When paired with broader risk management efforts, this approach strengthens overall defenses.
By combining robust supplier evaluations, effective patching processes, and secure sourcing, organizations can significantly enhance grid security. Key measures like vendor due diligence, mandatory multi-factor authentication, and continuous SIEM (Security Information and Event Management) monitoring help create a layered defense system. As Joe Saunders, CEO of RunSafe Security, warns:
"Across the power sector, the greatest cyber risk sits in the software supply chain and the third-party components woven through both IT and OT environments".
To safeguard substations, cybersecurity must be treated not as a secondary concern but as a strategic priority that ensures the resilience of critical infrastructure.
FAQs
How can we tell if a vendor is a supply chain cyber risk?
To determine whether a vendor might introduce cyber risks to your supply chain, take a close look at their cybersecurity practices, risk management strategies, and the security measures built into their products and systems. Any gaps in these areas could open the door to cyberattacks. Prioritize working with vendors who demonstrate strong, well-established protocols to reduce potential weak points.
What’s the fastest way to reduce risk from legacy substation devices?
The quickest way to minimize risks from outdated substation devices is by leveraging automated hardening frameworks. This approach involves actions like patching known vulnerabilities, installing firewalls, and diversifying components. The best part? These steps can be applied even if switching suppliers isn’t feasible.
How do we verify equipment isn’t counterfeit or compromised?
To keep your equipment safe from counterfeit or compromised items, it's crucial to adopt solid supply chain security practices. This means using trusted authentication methods, carefully evaluating suppliers, and conducting thorough integrity checks for both hardware and software. For example, validating firmware and software updates can help identify any malicious changes. Taking these precautions strengthens your defense against potential supply chain vulnerabilities.