
Why IEC 62351 Matters for Automation Security
Share
Power grids are under constant threat from cyberattacks, making secure communication essential. IEC 62351 is an international standard designed to protect power systems by securing key protocols like IEC 61850, IEC 60870-5, and DNP3. It addresses vulnerabilities in older systems and integrates modern tools such as TLS encryption, X.509 certificates, and Role-Based Access Control (RBAC).
Here’s what you need to know about IEC 62351:
- Core Security Goals: Ensures confidentiality, data integrity, authentication, and availability.
- Protocol Coverage: Strengthens legacy protocols (e.g., IEC 60870-5) and high-speed systems like GOOSE.
-
Key Features:
- TLS encryption for secure data transmission.
- Digital signatures to prevent tampering.
- RBAC to limit access based on roles.
- Key management for cryptographic security.
- System-Wide Protection: Safeguards communication from control centers to field devices, ensuring operational reliability.
IEC 62351 for the cybersecurity of IEC 61850 substations and interactions with DER systems
sbb-itb-501186b
Security Goals of IEC 62351
IEC 62351 focuses on five main objectives: confidentiality, data integrity, authentication, non-repudiation, and availability. Together, these principles create a robust defense for power systems, particularly in medium voltage automation setups. Here's how these goals strengthen system security.
Data Integrity and Confidentiality
To protect TCP/IP communications, IEC 62351-3 employs TLS encryption for protocols like IEC 61850 and ICCP. For XML-based data exchanges, IEC 62351-11 uses X.509 signatures to validate file authenticity and offers optional encryption for sensitive configuration files.
Message tampering is addressed through Message Authentication Codes (MACs) and digital signatures. These tools ensure that altered messages are flagged and rejected. Jürgen Resch from COPA-DATA highlights the risks of manipulation:
A cybercriminal could hack a business's energy controller and change the threshold values of a reaction... They could maliciously lower the perceived voltage measurement... so the controller thinks the voltage is lower than what it really is. The controller would then increase the voltage at the customer site, exceeding tolerances and destroying power supplies.
System Availability and Reliability
Ensuring system availability means maintaining uninterrupted operations. IEC 62351-7 introduces Management Information Bases (MIBs) tailored for power systems, which allow operators to monitor networks using SNMP. These MIBs provide real-time insights into grid health, helping detect and address potential issues before they lead to outages.
Time synchronization is another critical factor for reliability. The standard enforces the use of Simple Network Time Protocol (SNTP) for IEC 61850 profiles. This ensures precise coordination among protective relays, circuit breakers, and monitoring devices. Without accurate timestamps, systems might misinterpret event sequences, potentially causing cascading failures or unnecessary equipment shutdowns.
Protection Against Cyber Threats
To combat cyberattacks, IEC 62351 employs several safeguards. Mutual X.509 authentication blocks man-in-the-middle attacks, while digital signatures and sequential tracking prevent spoofing and playback attacks, where attackers retransmit recorded messages.
Role-Based Access Control (RBAC), defined in IEC 62351-8, limits access based on user roles. Even if credentials are compromised, attackers are restricted to the permissions of the stolen account, minimizing potential damage.
For high-speed communication, VLAN tagging isolates critical traffic, reducing the risk of malicious command injections into the system.
Main Components of IEC 62351 for Medium Voltage Automation
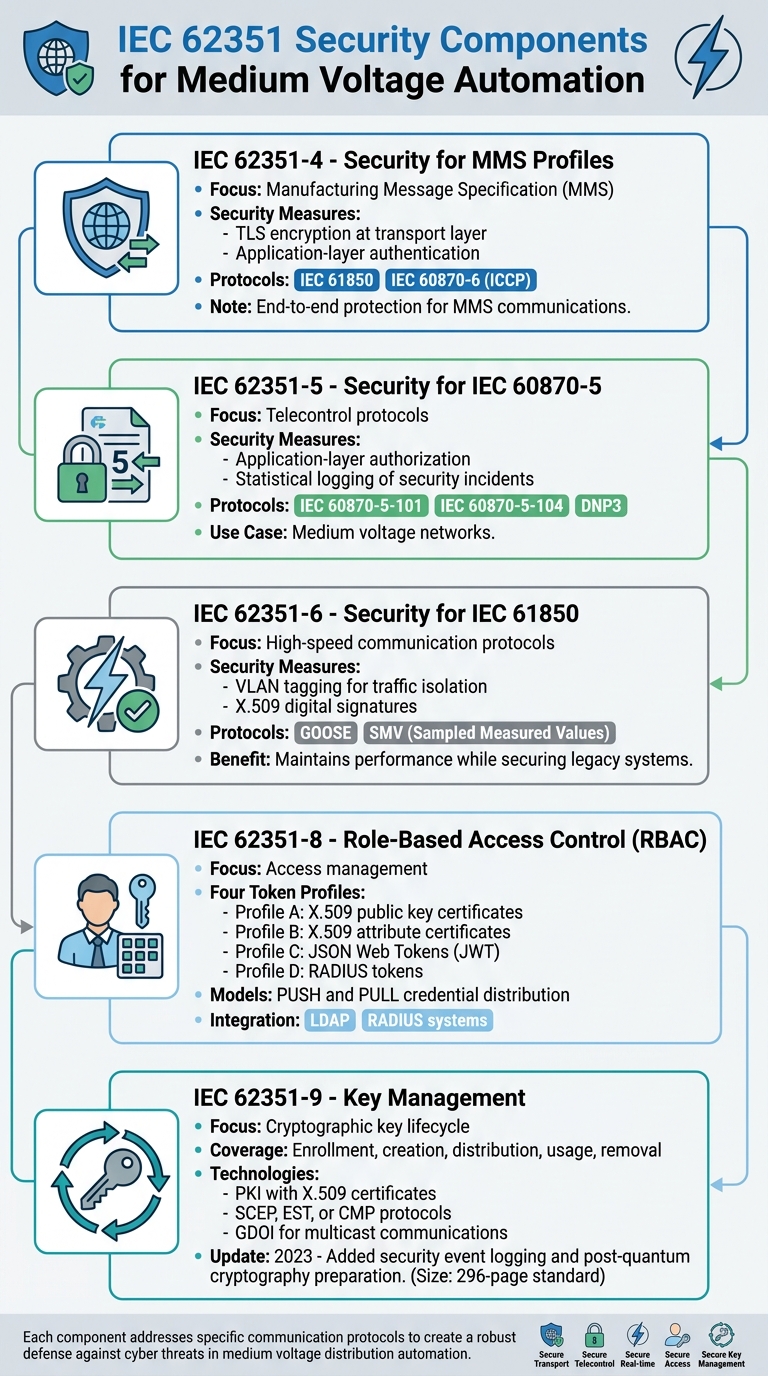
IEC 62351 Security Components for Medium Voltage Automation Systems
IEC 62351 includes various standards designed to secure medium voltage distribution automation. Each section of the standard addresses specific communication protocols, creating a robust defense against cyber threats. Here's how each component strengthens security.
IEC 62351-4: Security for MMS Profiles
The Manufacturing Message Specification (MMS), widely used in IEC 61850 and IEC 60870-6 (ICCP) systems, gains enhanced security through IEC 62351-4. This standard employs a dual-layer strategy: TLS encryption at the transport layer and application-layer authentication during handshakes and data transfers. Together, these measures ensure end-to-end protection for MMS communications. However, vulnerabilities remain a concern. In 2022, Team82 researchers identified five flaws in popular MMS implementations like libIEC61850 and the TMW IEC 61850 library. These vulnerabilities could allow remote code execution or cause devices to crash.
IEC 62351-5: Security for IEC 60870-5
IEC 62351-5 focuses on securing telecontrol protocols such as IEC 60870-5-101, IEC 60870-5-104, and DNP3, which are commonly used in medium voltage networks. It emphasizes application-layer authorization to safeguard critical substation resources. Additionally, it introduces statistical logging of security incidents, enabling operators to detect and respond to potential threats more effectively.
IEC 62351-6: Security for IEC 61850
High-speed communication protocols like GOOSE (Generic Object-Oriented Substation Event) and SMV (Sampled Measured Values) cannot afford the latency introduced by TLS encryption. To address this, IEC 62351-6 recommends VLAN tagging to isolate critical traffic and X.509 digital signatures to ensure data integrity and authenticity. These measures help mitigate risks in legacy systems while maintaining the performance required for medium voltage automation.
IEC 62351-8: Role-Based Access Control (RBAC)
IEC 62351-8 standardizes role-based access control through four token profiles:
- Profile A: X.509 public key certificates
- Profile B: X.509 attribute certificates
- Profile C: JSON Web Tokens (JWT)
- Profile D: RADIUS tokens
The framework supports both PUSH and PULL models for distributing credentials and integrates with systems like LDAP and RADIUS. This approach ensures that both human users and automated agents have access limited strictly to their roles and responsibilities.
IEC 62351-9: Key Management
Encryption relies on secure cryptographic key management, and IEC 62351-9 provides a comprehensive framework for this. It covers the entire lifecycle of cryptographic keys, including enrollment, creation, distribution, usage, and eventual removal. For asymmetric key management, it uses Public Key Infrastructure (PKI) with X.509 certificates and supports enrollment protocols like SCEP, EST, or CMP. In multicast communications, typical in distribution automation, the standard employs Group Domain of Interpretation (GDOI) to manage symmetric group keys, safeguarding GOOSE, Sampled Measured Values, and Precision Time Protocol traffic.
The 2023 update introduced security event logging for key management activities, linking these logs to IEC 62351-14 for centralized cybersecurity monitoring. It also anticipates the need for post-quantum cryptography, ensuring long-term resilience. This 296-page standard reinforces the goals of data integrity and system reliability.
How IEC 62351 Improves Medium Voltage Automation Security
Fixing Vulnerabilities in Medium Voltage Systems
Medium voltage automation systems were developed in a time when cybersecurity wasn’t a priority. Many older energy meters, switches, and substation controls relied on basic password protection, leaving them exposed to today’s sophisticated cyber threats. IEC 62351 steps in to address these shortcomings by enhancing older protocols like IEC 60870-5, DNP3, and IEC 61850 with modern security measures. These updates are designed to ensure data integrity and protect against cyber attacks.
One of the key risks it mitigates is the potential for physical damage caused by cyber manipulation. For example, a hacker could alter threshold values or spoof voltage readings in a SCADA platform, prompting a controller to increase voltage beyond safe limits, potentially damaging equipment. IEC 62351 counters such threats using digital signatures and TLS encryption to ensure data integrity and prevent unauthorized changes.
The standard also tackles issues like eavesdropping, replay attacks, spoofing, and unauthorized access. For time-sensitive communications such as GOOSE and Sampled Values, it incorporates replay protection through state-machine-based mechanisms and Layer-2 security. This layered approach allows even older systems to align with modern security standards without needing a complete hardware overhaul.
Beyond securing individual components, IEC 62351 extends its protections to cover the entire utility network.
Network-Wide Security for Utility Systems
In addition to improving component-level security, IEC 62351 ensures robust protection across the entire utility network. It safeguards communication from control centers to individual sensors and actuators in substations. Using X.509 certificates and Transport Layer Security (TLS), the standard enforces mutual authentication and encryption for end-to-end security. This ensures that every communication point is both verified and protected.
Another critical area IEC 62351 addresses is time synchronization. By securing the Simple Network Time Protocol (SNTP) as outlined in IEC 62351-6, utilities can maintain accurate and reliable protection systems. The standard also introduces Role-Based Access Control (RBAC) under IEC 62351-8, enabling centralized management of user permissions. This ensures access to substation resources is restricted based on the principle of least privilege. Centralized access control reduces the risk of credential misuse while ensuring consistent security policies across the network.
"The arrival of the IEC 62351 filled a huge void for energy security, bringing the existing non-secure communication protocols up to speed."
– Jürgen Resch, October 2019
How to Implement IEC 62351 in Automation Systems
Conducting a Risk Assessment
Start by evaluating your current infrastructure to pinpoint vulnerabilities. Map out your IT setup, paying close attention to critical communication points like substation control centers and automation systems. This step helps identify which parts of your network are most susceptible to cyber threats.
Next, review the protocols in use. Many medium-voltage systems still rely on outdated protocols that lack encryption and authentication. Look for specific risks, such as data manipulation, where attackers could alter voltage readings or threshold settings. Additionally, examine access control mechanisms. Systems that depend solely on basic passwords for devices like energy meters and switches are particularly vulnerable to unauthorized access.
For systems requiring time-sensitive communications, confirm whether Layer-2 protection and replay prevention are necessary. Lastly, assess your organization's ability to handle cryptographic processes, including the enrollment, distribution, and revocation of X.509 certificates. Use the table below to align your protocols with the relevant parts of IEC 62351:
| IEC 62351 Part | Focus Area for Risk Assessment | Relevant Protocols |
|---|---|---|
| Part 3 | End-to-end data protection (TLS) | TCP/IP-based connections |
| Part 4 | MMS-based security | IEC 61850, IEC 60870-6 (ICCP) |
| Part 5 | Application layer security | IEC 60870-5 (101/104), DNP3 |
| Part 6 | Layer-2 and Replay protection | IEC 61850 (GOOSE, Sampled Values) |
| Part 8 | Access Control | RBAC for all system users/agents |
| Part 9 | Key Management | Lifecycle of certificates and keys |
Once vulnerabilities are identified, you can begin implementing IEC 62351 measures to strengthen your existing protocols.
Integrating IEC 62351 with Existing Protocols
IEC 62351 is designed to enhance security in systems with older, less secure protocols, avoiding the need for a full system overhaul. To integrate it effectively, use TLS encryption for TCP/IP profiles (Part 3), application-layer security for MMS (Part 4), and digital signatures for GOOSE and Sampled Values (Part 6).
The division of tasks is crucial. Intelligent Electronic Devices (IEDs) and gateways should manage protocol-level protections, such as digital signatures and certificate handling. Meanwhile, network components like switches and routers should focus on segmentation and monitoring. Keep in mind that network hardware cannot substitute for protocol-level security, so ensure your IEDs and SCADA systems support these features.
Implement IEC 62351-8 for centralized, role-based access control (RBAC), replacing shared passwords with role-specific credentials. For multicast environments, such as synchrophasor networks, adopt Group Domain of Interpretation (GDOI) to streamline key management. Many energy automation platforms now integrate IEC 62351, enabling engineers to secure communications with TLS without disrupting operations.
Continuous Monitoring and Maintenance
Once IEC 62351 is in place, continuous monitoring becomes critical. Jürgen Resch from Copa-Data emphasizes:
"Applying IEC 62351 is not a one-time task. Once implemented, the security mechanisms need to be maintained and updated continuously, in line with changing security threats."
This means managing the entire cryptographic lifecycle, from certificate enrollment to removal. Automate certificate renewals and monitor revocations using Certificate Revocation Lists (CRL) or the Online Certificate Status Protocol (OCSP), as outlined in IEC 62351-9.
Leverage IEC 62351-7 for standardized monitoring through Simple Network Management Protocol (SNMP) and power-industry-specific Management Information Bases (MIBs). These tools help track the health and security of IEDs and communication lines across your network. Regularly update passwords, manage user roles via RBAC, and ensure only authorized personnel can access critical systems. For IEC 60870-5 systems, enable statistical logging of security events to maintain a detailed audit trail for forensic purposes.
Conclusion
IEC 62351 plays a vital role in protecting medium voltage automation by addressing key security areas like confidentiality, integrity, authentication, and non-repudiation. It safeguards critical utility protocols such as IEC 60870-5, IEC 61850, and DNP3, ensuring secure communication across power systems.
What sets IEC 62351 apart is its protocol-specific approach, which adapts security measures to the unique demands of power system communications. This ensures both the immediate protection of data exchanges and the long-term stability of operations.
By incorporating detailed risk assessments and integrating seamlessly with existing protocols, IEC 62351 enhances both security and operational performance in utility networks. Features like automated key lifecycle management reduce the effort needed for certificate distribution and revocation. Meanwhile, standardized monitoring through SNMP and utility-specific MIBs delivers real-time updates on device health and security. Centralized Role-Based Access Control (RBAC) simplifies managing access across a wide range of devices.
As the boundaries between IT and OT continue to blur, combining these security measures is essential. By doing so, IEC 62351 not only addresses today’s cybersecurity challenges but also prepares utilities for future threats. According to IPCOMM, “IEC 62351 is the current standard for security in energy management systems and associated data exchange”. For utilities managing medium voltage automation systems, adopting this standard is a critical step toward safeguarding infrastructure while meeting the reliability and efficiency needs of modern power grids.
Whether you’re dealing with older serial protocols or deploying advanced substation automation, IEC 62351 provides a strong foundation to combat threats like eavesdropping, replay attacks, spoofing, and unauthorized access - challenges that grow as power systems become more interconnected.
FAQs
Which IEC 62351 parts should I implement first?
IEC 62351-1 lays the groundwork by offering an overview of the standard and introducing key IT security principles specifically tailored for power supply systems. Think of it as the "big picture" guide - helping you grasp the overall framework before diving into the technical details of individual protocols.
This section is essential because it establishes a shared understanding of how cybersecurity integrates with the unique needs of power systems. By starting here, you’ll have a solid foundation to build upon as you explore the more specific aspects of the standard.
How does IEC 62351 secure GOOSE and Sampled Values without adding latency?
IEC 62351 protects GOOSE and Sampled Values through a fixed-latency setup. This approach ensures message authentication and confidentiality while operating at wire speed. It achieves real-time communication within the 3 ms target, delivering stronger security without sacrificing performance or causing delays.
What do I need to manage X.509 certificates and cryptographic keys at scale?
To handle X.509 certificates and cryptographic keys on a large scale, having a solid Public Key Infrastructure (PKI) is essential. A PKI oversees the creation, distribution, revocation, and overall management of digital certificates and keys. This ensures secure operations while meeting industry standards such as IEC 62351.
