Ultimate Guide to Cybersecurity for Power Teams
Share
Cybersecurity in power distribution is no longer optional - it’s a necessity. With the energy sector ranking as the 4th most targeted industry globally, cyberattacks have surged, threatening essential infrastructure like power grids and fuel pipelines. From phishing to ransomware, threats are growing more sophisticated, and the transition to interconnected smart grids has widened the attack surface.
Key takeaways include:
- Rising Threats: Cyberattacks on energy providers more than doubled between 2020 and 2022. Physical attacks on grids increased by 70% between 2024 and 2025.
- Critical Incidents: The 2015 Ukraine power grid attack left 230,000 people without power. In 2021, a ransomware attack on Colonial Pipeline caused fuel shortages and a $4.4 million ransom payment.
- Vulnerabilities: Outdated SCADA systems, weak passwords, and supply chain risks are common entry points for attackers.
- Compliance Risks: Failing to meet standards like NERC CIP can result in fines of up to $1 million per violation per day.
- Solutions: Focus on asset inventories, network segmentation, multi-factor authentication, and workforce training. Use frameworks like NERC CIP, NIST CSF 2.0, or IEC 62443 to guide your security strategy.
Cybersecurity isn’t just about technology; it’s about building a culture of vigilance. This guide outlines practical steps to protect power systems, secure compliance, and ensure uninterrupted service delivery.
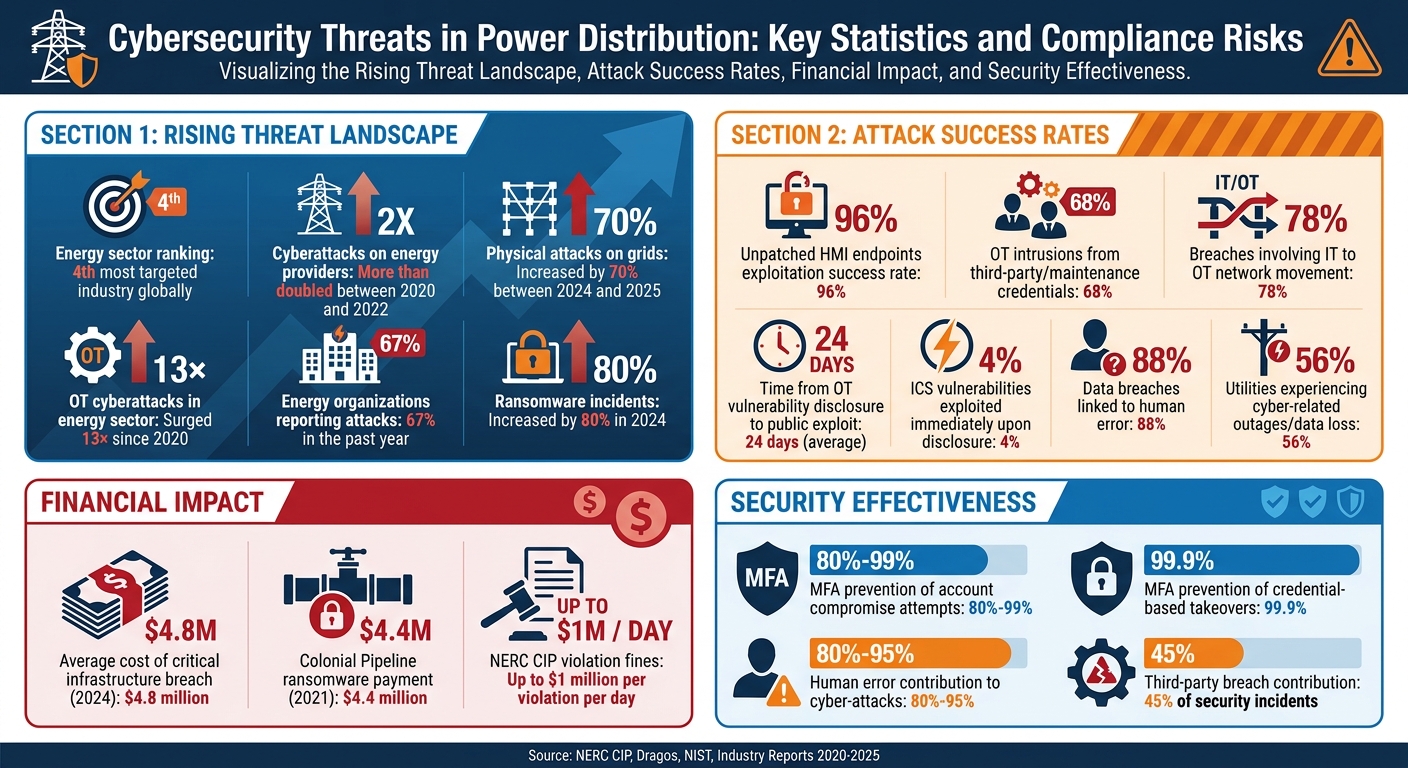
Cybersecurity Threats in Power Distribution: Key Statistics and Compliance Risks
Cyber Threats Targeting Power Distribution Systems
Types of Cyber Attacks
Cyber attackers exploit various vulnerabilities to target power distribution systems. One common tactic is phishing and credential theft, where attackers use fake emails to gain access to corporate networks or steal VPN passwords, granting them entry into critical systems. Once inside, they may deploy ransomware to encrypt operational technology (OT) data, forcing systems to shut down to prevent further damage.
Another significant threat comes from ICS-specific malware, such as Industroyer and BlackEnergy. These programs are designed to manipulate industrial control protocols, enabling attackers to disable safety systems or trip circuit breakers. For example, in December 2025, the ELECTRUM group extended its attacks from Ukraine to Poland's energy infrastructure, marking the first major global assault on Distributed Energy Resources. Meanwhile, Distributed Denial of Service (DDoS) attacks can flood control networks with excessive traffic, disrupting monitoring systems and making it impossible for operators to respond to grid issues in real time.
Supply chain attacks are also on the rise. These involve embedding malicious code in legitimate software updates or third-party hardware, bypassing traditional defenses. Alarmingly, 68% of OT intrusions stem from third-party or maintenance software credentials. Attackers often use legitimate tools that blend into normal operations, making them harder to detect.
"Electric environments are not being 'breached' loudly at a point in time; they are being inhabited silently over time." - Dragos
The speed of weaponizing vulnerabilities is staggering. On average, it takes just 24 days from the disclosure of an OT vulnerability to the availability of a public exploit. Even more concerning, 4% of ICS vulnerabilities are actively exploited as soon as they're publicly disclosed.
These tactics highlight the unique risks faced by systems like SCADA, which have their own specific challenges.
SCADA System Security Weaknesses
Supervisory Control and Data Acquisition (SCADA) systems are particularly vulnerable due to several inherent issues. Many rely on outdated operating systems like Windows XP or unpatched Windows 7, which cannot receive updates without vendor approval - leaving them permanently exposed. Since 2020, OT cyberattacks in the energy sector have surged 13×, with unpatched HMI endpoints showing a 96% success rate for exploitation.
Additionally, standard communication protocols like MODBUS, DNP3, and IEC 60870-5 often lack encryption or authentication, making it easy for attackers to intercept data or inject malicious commands. Remote access systems frequently rely on weak passwords without multi-factor authentication, further compounding the problem. In fact, 78% of breaches in the energy sector involve attackers moving from IT to OT networks.
"Today, a modern SCADA system (architecturally) looks more like a corporate IT network than a 'real-time' control system." - William T. Shaw, Cyber Security Consulting
Another overlooked risk lies in Computerized Maintenance Management Systems (CMMS). When compromised, these systems provide attackers with valuable information, such as asset histories, maintenance schedules, and privileged access. Traditional IT security tools often fail in SCADA environments because they interfere with real-time processes, leaving operators blind to OT-specific threats.
Addressing these vulnerabilities requires tailored training and focused security measures to tackle real-world OT challenges.
Compliance and Legal Risks
As cyber threats grow, so do the legal and compliance challenges for power operators. In North America, bulk electric system operators must adhere to NERC CIP (Critical Infrastructure Protection) standards, while European operators follow the NIS2 Directive. Failing to comply with NERC CIP standards can lead to fines of up to $1 million per violation per day.
One of the most commonly violated standards is CIP-007 (Systems Security Management), often due to poor patch management and inadequate logging. The average cost of a critical infrastructure breach reached $4.8 million in 2024. Beyond regulatory fines, non-compliance with measures like multi-factor authentication (MFA) or network segmentation can result in denied insurance claims or higher premiums.
| NERC CIP Standard | Focus Area | Compliance Risk |
|---|---|---|
| CIP-002 | BES Cyber System Categorization | Failure to document all critical cyber assets |
| CIP-007 | Systems Security Management | Most frequent violation; covers ports, patching, and access |
| CIP-008 | Incident Reporting | Legal issues for failing to report breaches or attempts |
| CIP-013 | Supply Chain Risk Management | Liability for unmonitored vendor access |
Under NERC CIP-013, utilities are required to log and manage all vendor and contractor access, making the supply chain a significant liability if credentials are compromised. Similarly, the EU's NIS2 Directive mandates strong security measures and rapid reporting of cyber incidents. Repeated incidents not only damage public trust in grid reliability but also invite stricter legislative oversight and increased political pressure.
To mitigate these risks, organizations must implement robust training programs and enforce clear security policies tailored to OT environments.
sbb-itb-501186b
NERC CIP Cybersecurity: A Deep Dive into Power Grid Protection and Beyond
Creating a Cybersecurity Framework for Power Teams
Building a cybersecurity framework for power distribution requires more than just firewalls and antivirus software. With 67% of energy organizations reporting attacks in the past year and ransomware incidents increasing by 80% in 2024, utilities need a structured plan that covers both IT and operational technology (OT) environments. Start by creating an asset inventory, categorizing generation, transmission, and distribution assets based on their risk levels. Use network segmentation techniques, such as industrial firewalls, VLANs, or data diodes, to block lateral movement between corporate IT systems and critical control systems.
Next, focus on system hardening. This includes regularly updating software and firmware for SCADA and ICS devices, disabling unused services and ports (like Telnet), and changing default credentials. Implement multi-factor authentication (MFA) for all remote and high-privilege logins - this simple step can prevent 80% to 99% of account compromise attempts. Deploy OT-aware IDS and SIEM tools for continuous monitoring, enabling real-time anomaly alerts and establishing normal baselines.
To maintain effectiveness, validate the framework regularly. Conduct vulnerability assessments, penetration testing, and red/blue/purple team exercises to assess defenses. Since human error or credential misuse contributes to 60% to 95% of breaches, workforce training and simulated incident response drills are equally important.
Once the framework is in place, defining clear team roles becomes the next priority.
Cybersecurity Team Roles and Responsibilities
Protecting power systems relies on clearly defined roles across IT, OT, and compliance functions. IT/OT Security Leads and CISOs ensure NERC CIP standards and zero-trust principles are integrated into system design. They also oversee strategic decisions and incorporate cybersecurity into enterprise risk management. Operations Directors and Chief Engineers focus on embedding security into daily maintenance operations, ensuring compliance at every step.
Compliance Officers manage NERC CIP documentation, such as personnel training records (CIP-004) and configuration change logs (CIP-010). System Administrators enforce MFA, manage session timeouts, and configure automatic lockouts for repeated login failures. Maintenance Technicians adhere to Role-Based Access Control (RBAC) protocols, accessing only assigned assets and documenting their work for audits. SOC Analysts monitor IDS and centralized logs for anomalies, while Incident Response Experts follow predefined playbooks to quickly restore operations after incidents.
Third-party access must be tightly controlled to mitigate OT intrusion risks. External partners should operate under time-limited, scope-restricted access sessions that are logged and reviewed as part of supply chain risk management plans (CIP-013). Permanent credentials should never be issued to third-party technicians; instead, use sessions that automatically expire.
| NERC CIP Standard | Responsibility Focus | Role Involvement |
|---|---|---|
| CIP-002 | Asset Categorization | IT/OT Leads, Operations Directors |
| CIP-004 | Personnel & Training | Compliance Officers, All Personnel |
| CIP-005 | Electronic Security Perimeter | Network Admins, IT/OT Security Leads |
| CIP-007 | Systems Security Management | System Admins, Maintenance Technicians |
| CIP-010 | Config Change Management | Chief Engineers, Maintenance Technicians |
| CIP-013 | Supply Chain Risk Management | Compliance Officers, Third-Party Vendors |
Clear roles not only ensure compliance but also streamline incident response for power systems.
Choosing Cybersecurity Frameworks
The choice of a cybersecurity framework depends on regulatory requirements and the operational environment. In North America, NERC CIP is mandatory for bulk electric system operators, addressing asset categorization, physical and cyber perimeters, and emergency response. In Europe, the EU NIS2 Directive mandates minimum security standards, supplier safeguards, and rapid breach notification. For OT-heavy environments, IEC 62443 provides detailed guidance on security zones, conduits, and technical requirements for control systems.
NIST CSF 2.0 offers a flexible, voluntary framework suitable for global use. The updated version includes a "Govern" function to align cybersecurity with enterprise risk management and uses "Profiles" to tailor controls to specific organizational goals. Many utilities map mandatory NERC CIP requirements to voluntary NIST or ISO/IEC controls to ensure both compliance and comprehensive security. ISO/IEC 27001 supports broader risk management and includes a sector-specific supplement, 27019, tailored for the energy industry.
| Framework | Scope / Mandatory? | Key Focus |
|---|---|---|
| NERC CIP | North America / Mandatory | Bulk electric system protection; asset categorization, personnel security, and emergency response |
| NIST CSF 2.0 | Global / Voluntary | Broad IT/OT risk management; six core functions including Govern, Identify, Protect, Detect, Respond, Recover |
| IEC 62443 | Global / Voluntary | OT/ICS specific; defines security zones, conduits, and technical requirements for control systems |
| EU NIS2 | European Union / Mandatory | Mandatory risk management, breach notification, and strict supplier safeguards for energy operators |
A defense-in-depth approach, combining physical, administrative, and technical controls, is critical for resilience. NIST's Quick Start Guides can simplify CSF 2.0 implementation for common goals like risk management and workforce development. Transitioning from periodic assessments to continuous control monitoring (CCM) with automated, real-time oversight is key for long-term security.
The right framework sets the stage for effective training and awareness programs. Once selected, enforcing strong access control measures strengthens your security stance.
Access Control Methods for Power Systems
Access control defines who can interact with critical systems and what actions they can perform. Role-Based Access Control (RBAC) limits technicians to the assets and work orders assigned to their role, reducing the potential impact of compromised accounts. For example, maintenance staff can only access and update their assigned equipment, not the entire network.
Least-privilege access takes this further by granting users only the permissions necessary for their tasks. Combined with zero-trust architecture - which requires continuous identity verification for every user and device - this approach creates a more secure environment. Zero trust operates on the principle of "never trust, always verify", treating every access request as potentially suspicious.
Multi-factor authentication adds another layer of protection by requiring multiple proof points. In high-security environments, physical hardware security keys like YubiKey, which connect via USB or NFC, offer enhanced security. MFA can prevent 99.9% of credential-based account takeovers.
Additional measures include enforcing session timeouts and automatic lockouts after repeated login failures. All actions, such as logins, asset modifications, and work order entries, should be timestamped and attributed to specific users in immutable logs. This supports both NERC CIP compliance and forensic investigations. The Purdue Model can also help by creating logical security zones, isolating OT networks at substations and control centers from corporate IT systems. Industrial DMZs and data diodes provide physical separation to prevent malware from spreading between IT and OT environments.
Training and Awareness Programs for Power Teams
Human error is responsible for an overwhelming 80%–95% of cyber-attacks. This makes workforce training a critical layer of defense for power systems. While technical safeguards are essential, addressing human error through effective training programs is vital. In the energy sector, OT cyberattacks have increased 13-fold since 2020, with 68% of OT intrusions linked to third-party or maintenance software credentials. To combat these threats, power teams need ongoing, role-specific training that goes beyond basic compliance.
Incidents like the breaches in Ukraine and Colonial Pipeline highlight how human vulnerabilities can enable sophisticated attacks.
"The human element remains both the greatest vulnerability and the greatest opportunity in cybersecurity defense." – GDS Associates, Inc
Training must shift the focus from mere compliance to fostering a security-first mindset. Every employee, from executives to field staff, should understand their role in protecting the grid. Leadership involvement is key - when executives participate in phishing drills and training alongside their teams, it reinforces that cybersecurity is a shared responsibility, not just an IT issue. Training should cover both general and specialized topics, preparing every team member to respond to modern threats.
Required Training Topics
Power teams benefit from a mix of foundational security knowledge and specialized OT/ICS training. Phishing recognition is a must, as spear-phishing campaigns that use malware-laden Excel attachments continue to target utility workers. Realistic phishing simulations with immediate feedback help employees learn from mistakes.
Password hygiene training should emphasize creating passwords longer than 12 characters, using a mix of symbols, and relying on encrypted password managers instead of spreadsheets. Multi-factor authentication (MFA) is another essential safeguard, capable of preventing nearly all credential-based account takeovers. Employees should get hands-on experience with tools like hardware security keys and authentication apps to build their confidence.
Training on Zero Trust architecture is crucial, teaching employees to verify every access request, no matter its origin. For technical staff, SCADA-specific training is important for understanding vulnerabilities in supervisory control and data acquisition systems. This includes using the Purdue Model to segment OT networks from corporate IT systems. Technicians should also learn about patch management for legacy systems, focusing on risk prioritization and alternative controls when immediate updates aren’t possible.
Compliance with NERC CIP standards is a cornerstone for North American bulk power utilities. For instance, CIP-004 mandates training and background checks for anyone with electronic access to Bulk Electric System (BES) Cyber Systems. CIP-007 addresses monitoring, access controls, and malicious code prevention. Maintaining detailed training records and conducting regular audits are essential for compliance.
Given that 68% of OT intrusions originate from third-party credentials, supply chain and vendor risk management training is critical. Employees must enforce time-limited, scope-restricted access for external partners. Features like automatic session expiration and thorough logging help ensure that permanent credentials are never issued to third-party technicians.
Physical security also deserves attention. With physical attacks on power grids rising by 70% in a single year, training should include access control protocols, visitor escort procedures, and recognizing suspicious activity near critical facilities.
Incident response training prepares teams to act quickly during a breach. Cross-functional tabletop exercises - bringing together IT, OT, compliance, and leadership - simulate cyber incidents, identify gaps, and build confidence for high-pressure situations. Beyond structured training, ongoing awareness efforts are key to keeping skills sharp and maintaining a vigilant culture.
Building Security Awareness
Maintaining cybersecurity awareness requires more than annual training sessions. Continuous, engaging initiatives help counteract vigilance fatigue. Appointing department-level security champions creates visible advocates who lead by example and provide role-specific guidance. These champions make security policies practical and accessible for their teams.
Regular phishing simulations, using realistic email templates that mimic current threats, reinforce safe email practices. Positive reinforcement, such as publicly acknowledging employees who report suspicious emails, builds a culture of proactive security.
"Cybersecurity isn't just the IT department's job; it's everyone's responsibility, from the C-suite to the field technicians." – GDS Associates, Inc
Behavioral risk scoring identifies high-risk users, enabling targeted training for those who need it most. AI-powered learning platforms can tailor training content and difficulty based on individual performance, ensuring employees are challenged appropriately. Gamification elements, like leaderboards and badges, make training more engaging and memorable.
Clear, non-punitive reporting channels are essential for encouraging employees to report potential security issues without fear of blame. This proactive reporting helps Security Operations Centers (SOC) respond quickly to threats. Cross-sector collaboration with organizations like NERC, APPA, NRECA, E-ISAC, and CISA ensures utilities stay informed about new threats.
Role-specific workshops enhance awareness by addressing the unique responsibilities of control room operators, field technicians, and IT/OT specialists. Training programs must also evolve to reflect new adversarial tactics and recent incidents. Using examples from the energy sector makes training more relevant and highlights the real consequences of security failures.
Maintaining Cybersecurity in Power Systems
Keeping power systems secure isn’t a one-and-done deal. It takes ongoing vigilance and effort to tackle the ever-changing landscape of cyber threats. Three key areas demand attention: vulnerability assessments, threat intelligence, and regularly updated security policies.
Conducting Vulnerability Assessments
Vulnerability assessments are your first line of defense, helping you spot and address weaknesses before attackers can exploit them. With power systems becoming more interconnected, frequent scanning of both IT and OT environments is critical. Here's a sobering fact: the average time between the disclosure of an OT vulnerability and the appearance of a public exploit is just 24 days. That means fast action is non-negotiable.
Third-party assessments bring a fresh set of eyes to your systems. These independent evaluations can uncover blind spots and validate whether your current controls are doing their job. For instance, misconfigured devices or default settings can be a major risk, so auditing device configurations is a must.
A comprehensive inventory of all digital assets is the backbone of effective assessments. This includes everything from remote devices to "grid-edge" assets - like pole-mounted switches and underground vaults - which are often unmanned and physically vulnerable. Simulated attack exercises, such as red, blue, or purple team drills, can also test your response strategies under real-world conditions.
When it comes to fixing vulnerabilities, focus on the ones that pose the greatest risk. Not all issues are created equal, so prioritize based on actual exposure, especially for internet-facing systems and critical substation automation. Regularly checking your network segmentation can prevent breaches in corporate IT from spreading to OT systems. Automated scanning tools can help cover all the bases, but the real value lies in acting on the insights they provide.
"Independent cybersecurity assessments have become vital for preserving electricity system integrity." – Tripwire
Once vulnerabilities are identified, the next step is staying ahead of emerging threats with actionable intelligence.
Using Threat Intelligence
Threat intelligence shifts the focus from hypothetical risks to real-world dangers targeting your sector. Consider this: in late 2025, the group KAMACITE spent four months scanning industrial devices in the U.S., mapping control loops by targeting HMIs, variable frequency drives, and cellular gateways. Around the same time, another group, ELECTRUM, launched a major attack on Polish energy infrastructure, marking a global first for Distributed Energy Resources.
These incidents underline the importance of knowing your adversaries and preparing for their tactics. Modern attackers often lurk quietly in networks for extended periods rather than launching noisy, one-off attacks. This makes continuous monitoring an absolute necessity.
Participating in industry-specific information-sharing platforms like E-ISAC and CISA can be a game-changer. These groups allow utilities to share malware signatures and other indicators of compromise, helping everyone stay ahead of active threats. Considering that third-party breaches account for 45% of security incidents in the energy sector, keeping a close eye on vendor access and scoring their risks based on current intelligence is just as crucial.
Using OT-aware analytics to connect IT security data with OT historian data can help detect anomalies early. Drills based on real-world threat intelligence can make incident response simulations more effective. And when it comes to patching, prioritize systems that are internet-facing or connected to engineering workstations.
"Vulnerabilities do not become dangerous when they are disclosed, they become dangerous when they are exposed, reachable, and tied to systems that influence grid visibility and control." – Dragos Intelligence Fabric
As new threats emerge, security policies must be updated to keep pace.
Updating Security Policies
Static security policies are a recipe for disaster, especially when 67% of energy organizations reported a cyberattack in the last year. Policies need to evolve as quickly as the threats they aim to counter.
Aligning with frameworks like NERC CIP, NIST CSF 2.0, ISO 27001, and IEC 62443 can help ensure compliance while strengthening security. For example, the NIST CSF 2.0 "Govern" function integrates cybersecurity into enterprise risk management, pushing it beyond just technical guidelines to a leadership-level priority.
Instead of relying on periodic manual assessments, shift toward continuous monitoring of both IT and OT environments. Automated Governance, Risk, and Compliance (GRC) platforms can streamline this process by managing multiple frameworks from a single dashboard, automating evidence collection, and flagging policy gaps as they arise.
Incident response playbooks should also be updated regularly to reflect new threats and operational changes. Access policies should require multi-factor authentication for all remote and high-privilege logins, significantly reducing the risk of credential-based attacks. For third-party vendors, implement risk-based classifications to ensure they meet standards like IEC-62443 when accessing critical systems.
To ensure policies are effective, validate them through regular penetration tests, red team exercises, and security audits. Testing ensures that what’s written on paper actually holds up in practice.
"Network operators must remain adaptive and committed to continuous improvement in their cybersecurity posture." – Tripwire
Conclusion
Cyber threats are evolving rapidly, making strong cybersecurity measures critical for maintaining grid reliability. With 88% of data breaches linked to human error and 56% of utilities experiencing cyber-related outages or data loss, it’s clear that employees play a dual role - they can be your greatest risk but also your most valuable defense.
Creating a strong cybersecurity foundation requires three key elements: ongoing training that goes beyond basic compliance, structured frameworks like NERC CIP, NIST CSF, and IEC 62443 to guide security practices, and active maintenance through regular assessments, threat intelligence, and policy updates.
Real-world cases have shown that technology alone can’t safeguard critical infrastructure. As GDS Associates notes:
"Educated, engaged, and security-aware employees are the most cost-effective cybersecurity investment utilities can make".
A defense-in-depth strategy adds multiple layers of protection - such as network segmentation, multi-factor authentication, offline backups, and continuous monitoring. Each layer acts as a safety net, ready to catch threats if another fails. Coupling this with participation in information-sharing platforms like E-ISAC ensures your organization stays ahead of emerging dangers, including AI-driven phishing and specialized ICS malware.
The energy sector is the 4th most targeted industry globally, with cyber attacks on energy providers more than doubling between 2020 and 2022. A proactive response is essential. Embedding cybersecurity into your organizational culture - from field teams to executives - shifts the focus from compliance to resilience, empowering your workforce to act as your strongest defense.
Securing power distribution requires investing in both people and technology. By integrating these strategies into every level of your organization, you can build resilience that goes beyond compliance. For more guidance on protecting electrical equipment and power distribution systems, check out the resources offered by Electrical Trader.
FAQs
Where should a power team start with OT cybersecurity?
Power teams should prioritize foundational training for OT operators, focusing on cybersecurity risks and practical strategies to mitigate them. This training should be tailored to the specific operational environment, ensuring it resonates with real-world scenarios. Using immersive learning techniques can help operators better understand and handle potential threats effectively.
Beyond training, it's essential to establish a robust security framework. Start by assessing risks and gaining a clear understanding of the OT infrastructure. From there, integrate layered defenses into daily operations. This approach not only helps pinpoint vulnerabilities but also equips teams to respond swiftly to cyber threats, safeguarding critical power systems.
How can we secure legacy SCADA systems we can’t easily patch?
To protect older SCADA systems that are difficult to update, focus on strategies such as network segmentation, continuous monitoring, and role-based access controls. By segmenting the network, you can reduce the risk of threats spreading across systems. Continuous monitoring helps identify suspicious activity without needing to modify the system itself. Role-based access ensures that only approved individuals can access or manage critical components. Additionally, close cooperation between IT and OT teams is essential to tackle the specific weaknesses these systems may have.
What’s the fastest way to reduce vendor and remote-access risk?
The fastest way to reduce risks tied to vendors and remote access is by rolling out robust cybersecurity training and maintaining ongoing awareness programs for your team. On top of that, make sure you have secure remote access protocols in place and set up clear incident response procedures to handle any potential threats swiftly and effectively.